This guide will show you how to troubleshoot or validate Windows Desktop MFA - EJBCA configuration.

API User for ReST API authentication
A separate EJBCA user (End Entity) with limited privileges improves the overall security posture of EJBCA deployment. The following options will provide you the detail on the bare minimum Options in Roles and Access Rules in EJBCA to be chosen for the API user created.
- Login to EJBCA Administration GUI
- Navigate to
System Functions->Roles and Access Rules - Add a new Role or any existing role you want to use
- For the bare minimum, Access Rules required
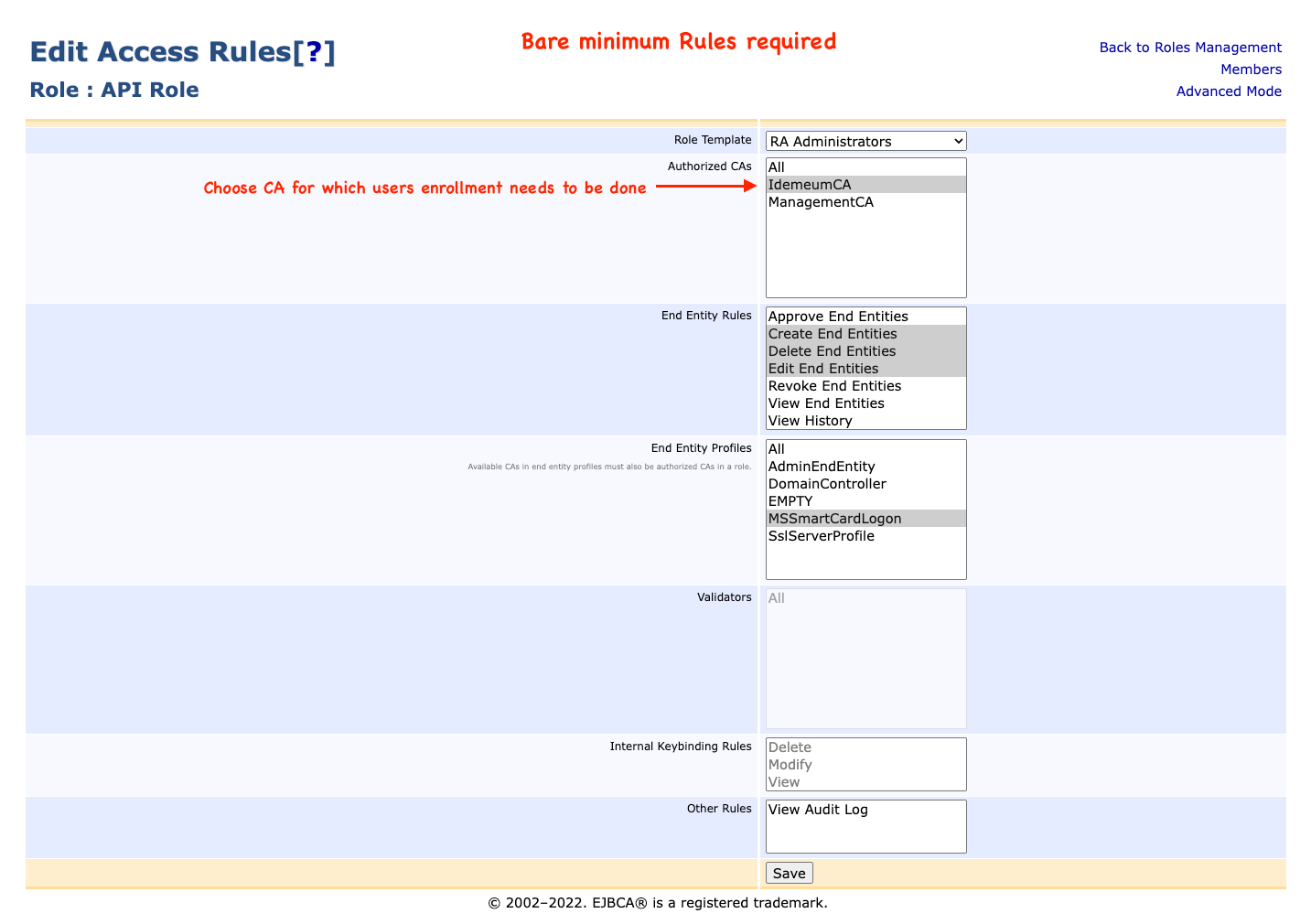
- Click
Save - Click
Advanced ModeChoose the options as shown below

- Click
Save - Click
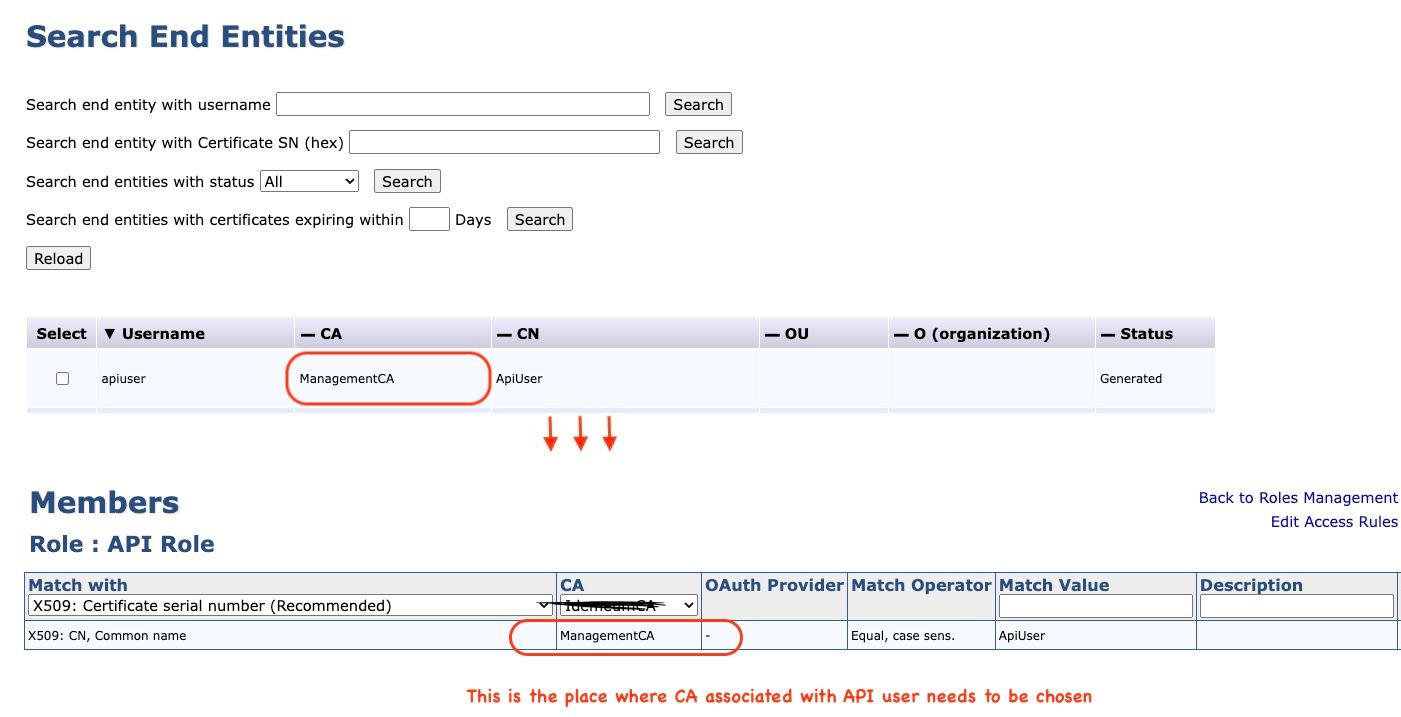
Members - In the example below ApiUser is the End Entity created. IdemeumCA is the CA for which User Certificate needs to be enrolled
Validate user enrollment
This step validates
- API keystore and password used for authentication meet the desired expectation for enrolling the user cert.
- Able to generate user cert for the profiles configured
- The end entity used for API authentication has the right Role access
Pre-requisites:
Download and install Java. Please click here to download
java -jar erce-0.0.6.jar enroll genkeys --endentityprofile=MSSmartCardLogon --certificateprofile=MSSmartCardLogon --ca= --subjectaltname="upn=testuser@" --subjectdn="CN=testuser" --username=testuser --password=testuser --keyalg=RSA --keyspec=2048 --authkeystore= --hostname= -akpCommand output:
End entity with username testuser has succesfully been enrolledThe above command will generate an testuser end entity/user in EJBCA.
Validate end-entity certificate in Domain Controller
This step validates the end entity/user-generated in the previous step is valid when the same cert is presented to the domain controller during virtual smart card logon.
- Login to EJBCA Administration GUI
- Navigate
RA Functions->Search End Entities Search end entity with usernameentertestuser- Click
Search - Click
Viewnext toCertificates - Click
Download to Firefoxwhich downloads.cerfile
certutil -urlfetch -verify -seconds <.cer file>If there is an error in the revocation check, please try reaching the CRL distribution endpoint and make sure you can download CRL.
Command output:
Verified Issuance Policies: None
Verified Application Policies:
1.3.6.1.5.5.7.3.2 Client Authentication
1.3.6.1.4.1.311.20.2.2 Smart Card Logon
Cert is an End Entity certificate
Leaf certificate revocation check passed
CertUtil: -verify command completed successfully.Other useful commands
- Command to verify API keystore certificate is valid by comparing issuer and subject against server certificate.
Command 1:
openssl s_client -connect <hostname:port> | openssl x509 -noout -issuer -subject -purposeCommand 2:
openssl pkcs12 -in <p12 file API keystore> -clcerts -out cc.pem && openssl x509 -in cc.pem -noout -issuer -subject -purpose
The issuer should match, and the subject in case of Command 2 should match the CN of the end entity
As an alternative, you can view and compare cert by temporarily importing them to the Windows Certificate store.



