Capabilities overview
YouTrack is a proprietary, commercial browser-based bug tracker, issue tracking system and project management software developed by JetBrains. It focuses on query-based issue search with auto-completion, manipulating issues in batches, customizing the set of issue attributes, and creating custom workflows.
| Supported capability | Required plan | Details |
|---|---|---|
| Passwordless SSO | Any | Low SSO tax |
| Account creation with SAML | Any | SAML JIT (create accounts only) |
| Password manager | Any | Auto-fill / Auto-capture |
Prerequisites
In order to integrate idemeum with YouTrack you will first need to obtain SAML metadata parameters for your idemeum tenant. Specifically you will need:
- Identity Provider SSO URL
- Identity Provider Entity ID
- SHA256 Fingerprint of Public X509 certificate
Instructions for how to obtain these SAML metadata parameters are below.
Now you will need to use any online tool to calculate SHA256 fingerprint of your certificate. Input your certificate and obtain SHA256 hash value.
The example of SSL certificate SHA256 fingerprint is D2:F0:FA:B8:D0:56:7A:31:28:42:40:88:E1:BB:
88:4B:C5:2A:8F:A7:88:68:1F:EA:A9:29:00:C5:C7:66:2B:54
Passwordless Single Sign-On (SAML)
Configure SSO in YouTrack
- Using your admin credentials access your YouTrack portal
- Navigate to Settings -> Access Management -> Auth Modules
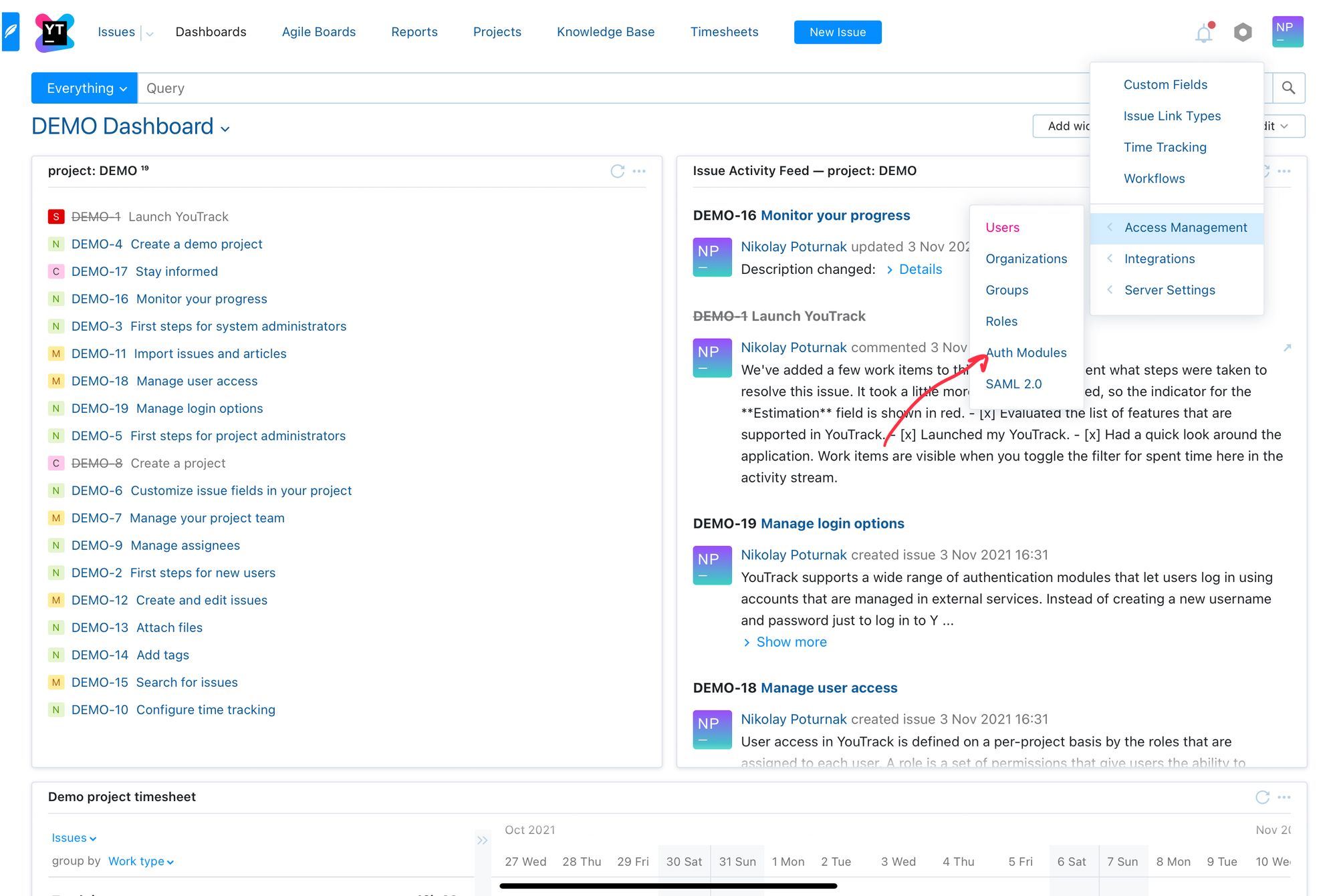
- Click New Module and then choose SAML 2.0
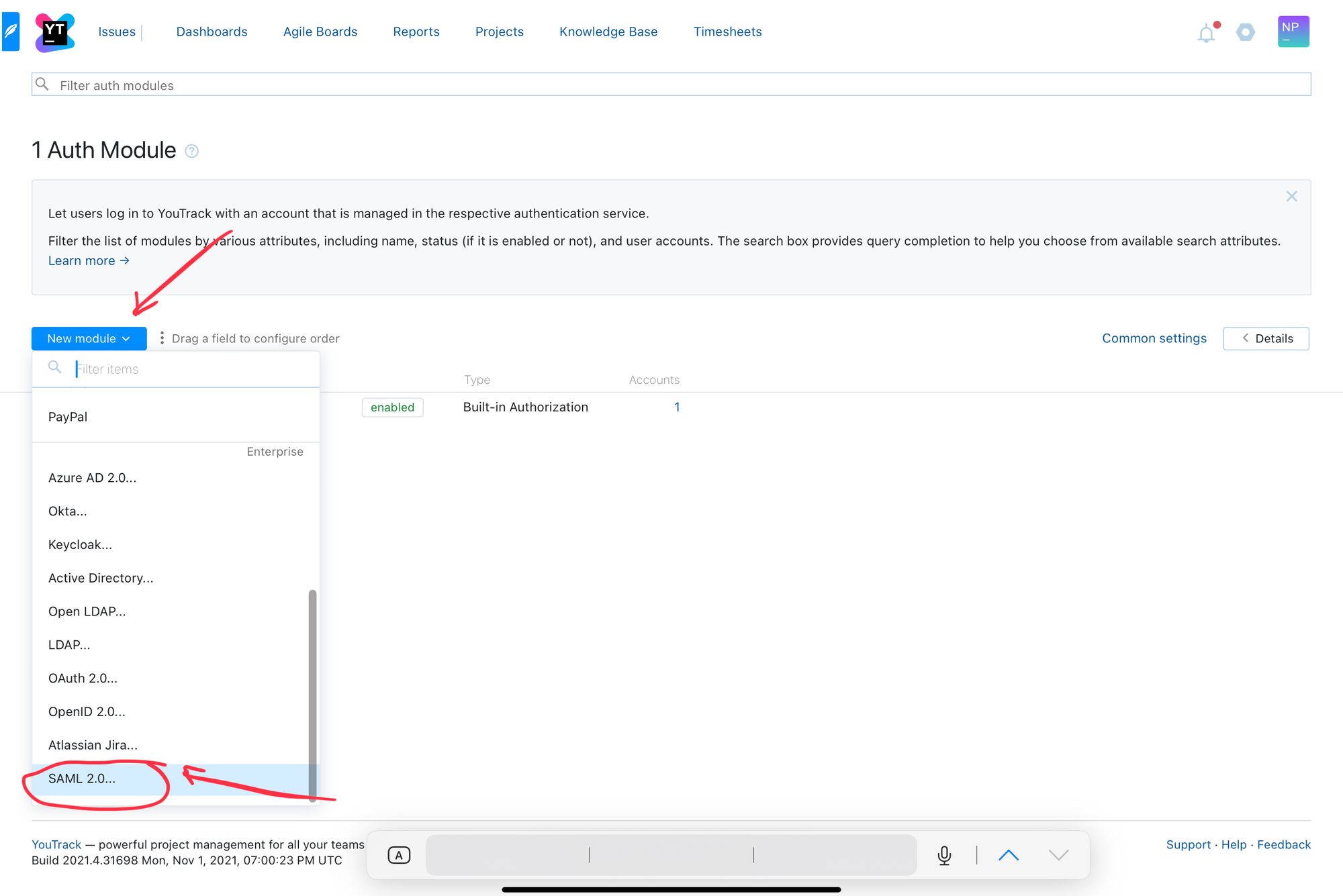
Now you will be using idemeum SAML values obtained in the prerequisites section
- Paste Identity Provider SSO URL into SAML SSO URL
- Paste Identity Provider Entity ID into IdP Entity ID
- Paste SHA256 fingerprint
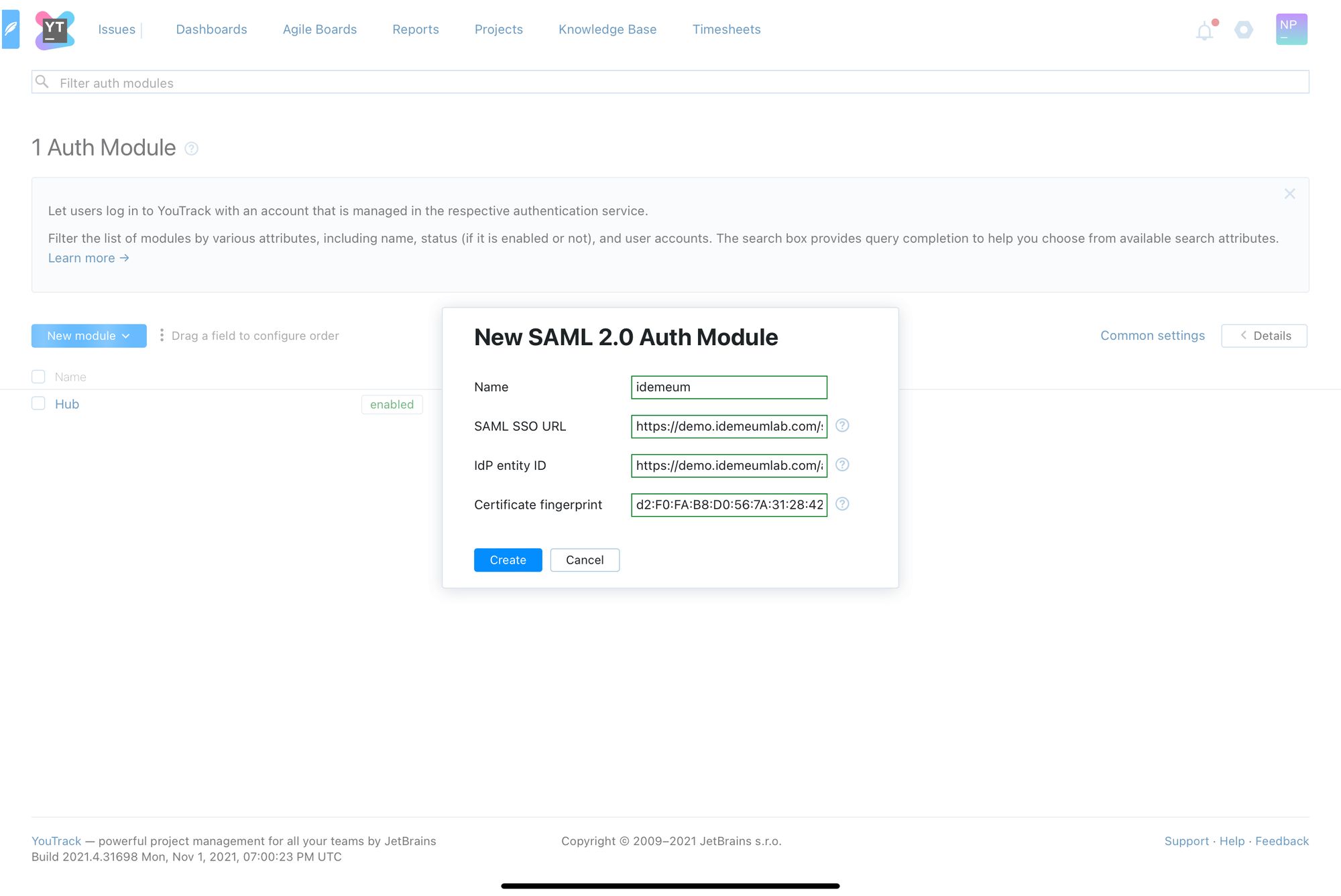
- Click Save
- Now you can obtain the values that we will need for idemeum configuration. We will need SP entity ID and ACS URL. Copy these values.
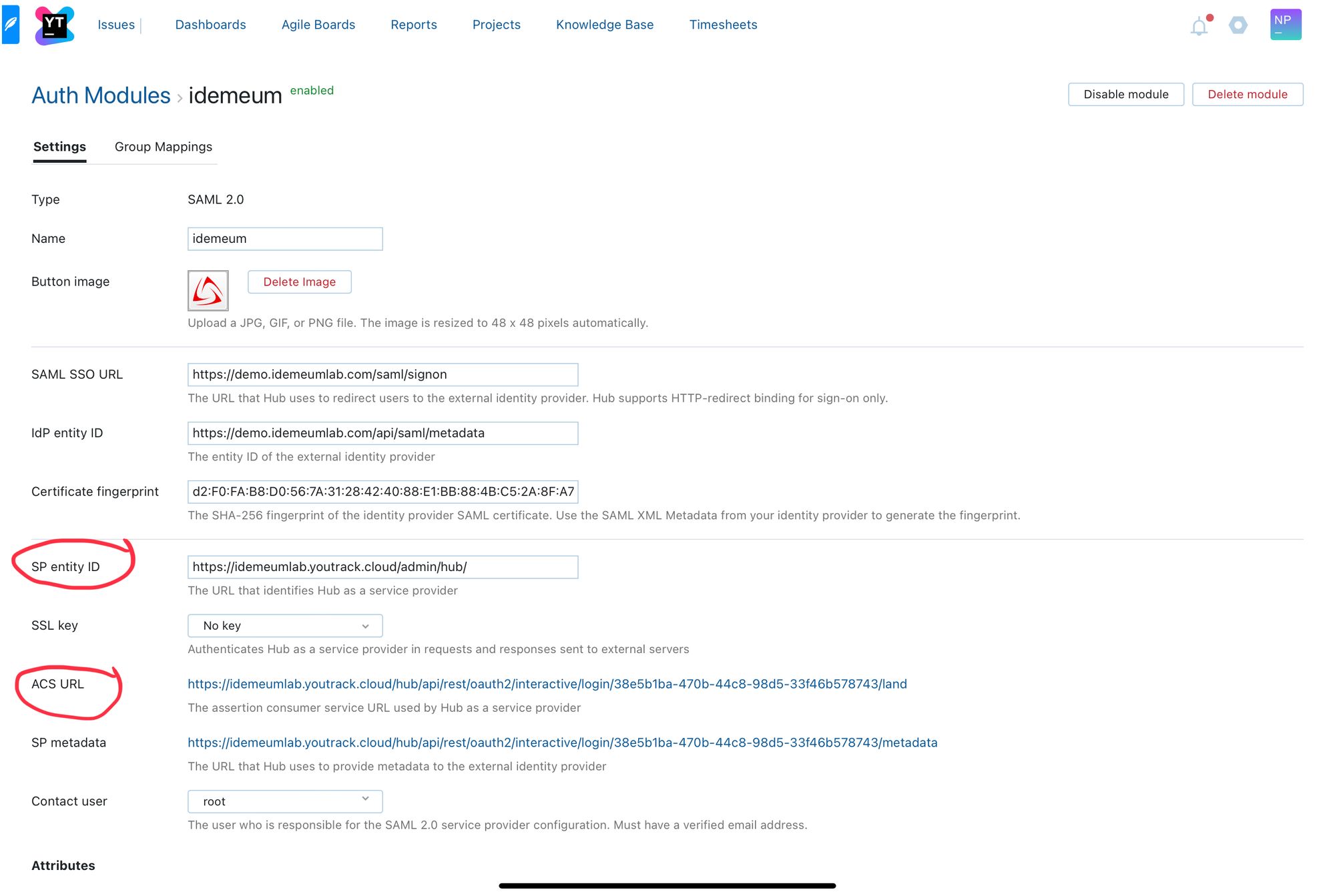
- You can now exit Auth Modules configuration
Assign all SSO users to a default role
When new users log into YouTrack with SSO they will not have access to anything in YouTrack. You will need to give these users permissions by assigning them to a role.
You have 2 options:
- You can create a group, say SSO users, and assign a certain role to this group. For instance, you can assign Developer role to SSO users group. Now you can configure your SAML2.0 Auth Module to automatically put SSO users into SSO users group.
- Another easy way is to leverage existing Registered Users group and assign a role to it. This way all new users will be part of this group and will be be given an assigned role.
You can navigate to Settings -> Access Control -> Groups to create groups and assign roles to them.
Configure SSO in idemeum
- Navigate to your idemeum admin portal at https://[your domain].idemeum.com/adminportal
- Click Applications in the left menu
- Search for YouTrack JetBrains application and click Add App
- Click SAML at the top navigation menu
Now you will be entering SAML metadata values obtained from YouTrack
- Paste ACS URL into Assertion Consumer Service URL
- Paste SP Entity ID into Audience URI
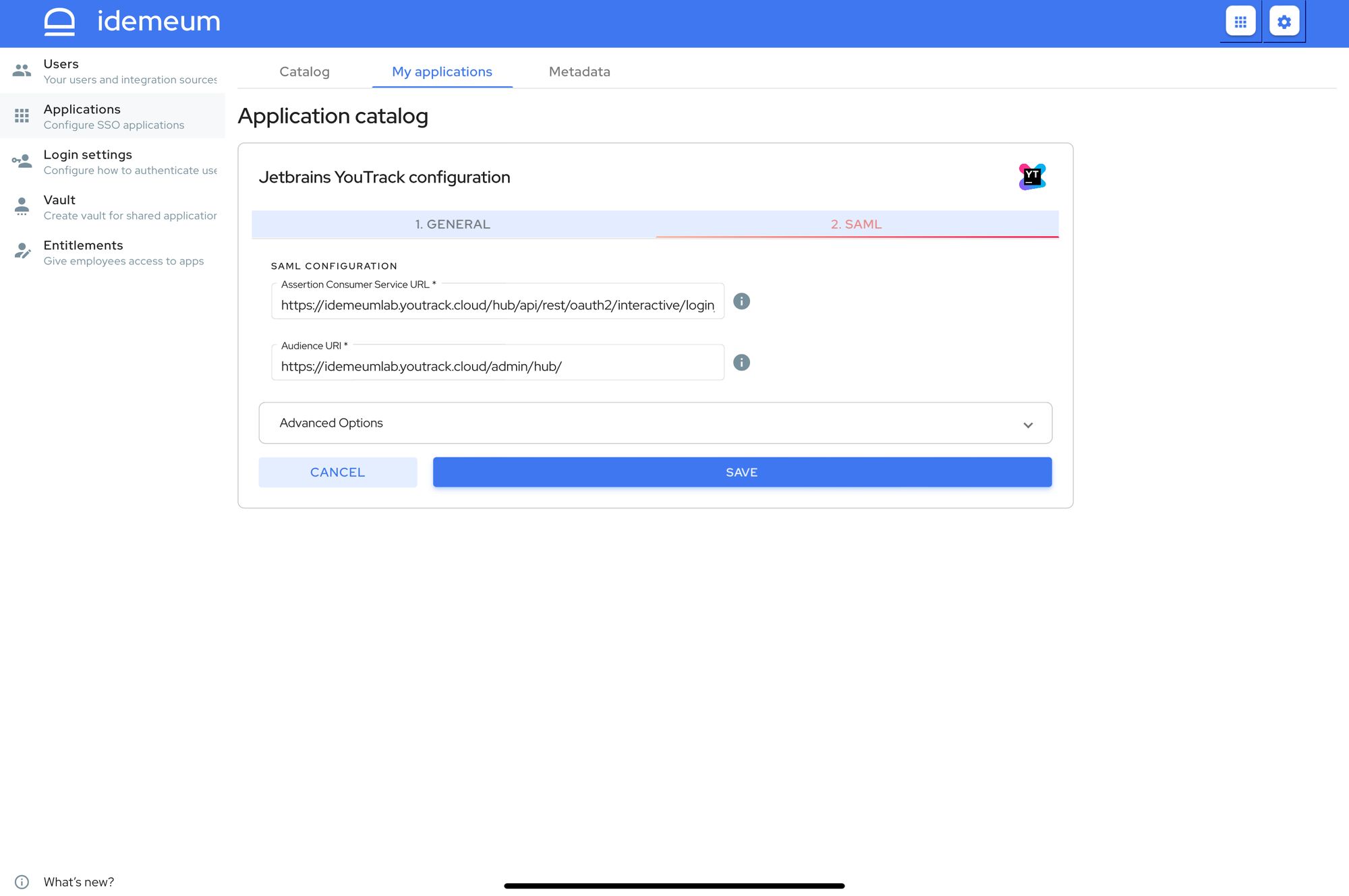
- Click Save
Account creation with SAML JIT
YouTrack currently supports account creation with SAML JIT - SAML Just-in-Time provisioning. When new users try to log in with passwordless SSO into YouTrack, the user account with be automatically created.
SAML JIT supports only account creation (no account deletion or updates).
Application entitlements
Before users can access applications you need to make sure you entitle applications to them. In idemeum admin portal navigate to Entitlements section to assign applications to your employees.
SAML SSO login flows
YouTrack supports both:
- IDP Initiated Flow
- SP Initiated Flow
IDP Initiated flow
With this flow users first navigate to idemeum user catalog and then click on YouTrack icon to launch application.
SP Initiated flow
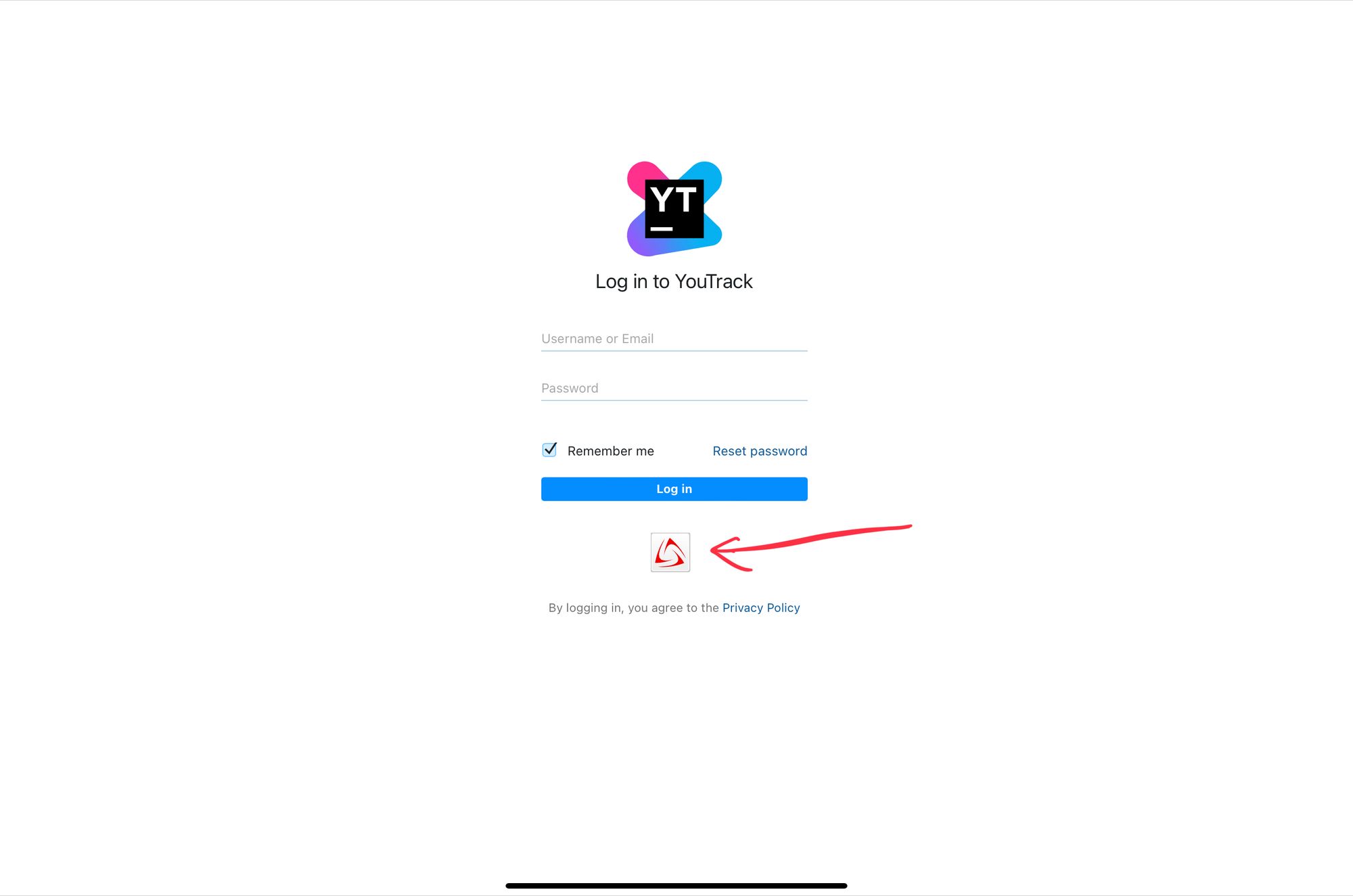
- Navigate to your YouTrack domain
- Click on the SSO icon to login with idemeum