Capabilities overview
GitLab is a web-based DevOps lifecycle tool that provides a Git repository manager providing wiki, issue-tracking and continuous integration and deployment pipeline features, using an open-source license, developed by GitLab Inc.
| Supported capability | Required plan | Details |
|---|---|---|
| Passwordless SSO | Free plan | Low SSO tax |
| Automated provisioning | Premium plan | SCIM 2.0 (create, remove accounts) |
| Password manager | Any | Auto-fill / Auto-capture |
Prerequisites
In order to configure passwordless SSO between idemeum and GitLab you will first need to obtain your idemeum tenant SAML metadata parameters. Specifically you will need:
- SHA1 formatted fingerprint of Public X509 certificate
- Identity Provider SSO URL
Instructions for how to obtain idemeum SAML metadata values for your tenant are below.
The example of SSL certificate SHA1 fingerprint is 66:6D:DF:74:A2:F9:98:5C:71:7D:BD:A0:06:91:8E:6E:44:BA:C9:90
Passwordless Single Sign-On (SAML)
Configure SSO in GitLab
- Navigate to your Groups in GitLab admin dashboard
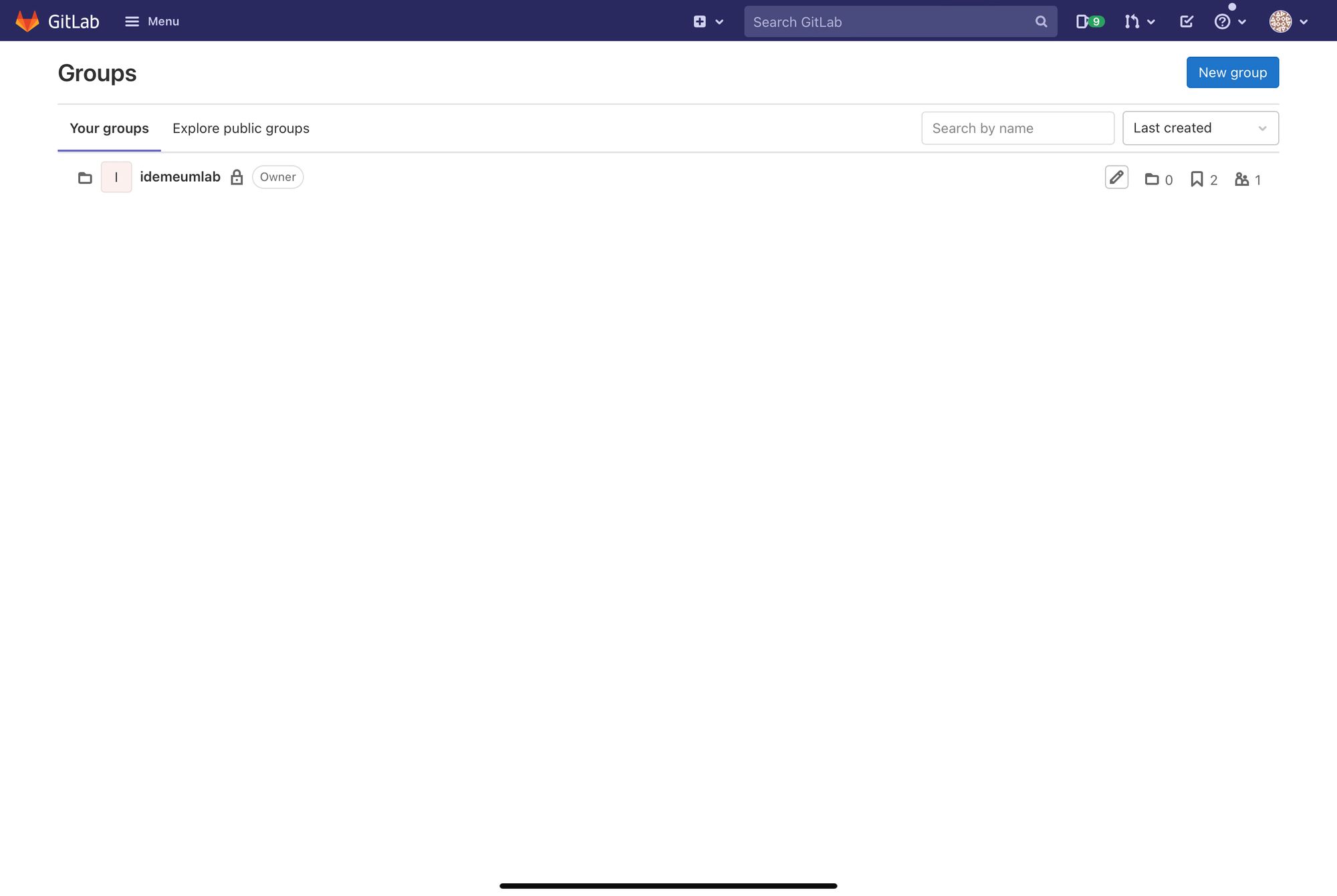
- Choose the group you want to enable SSO
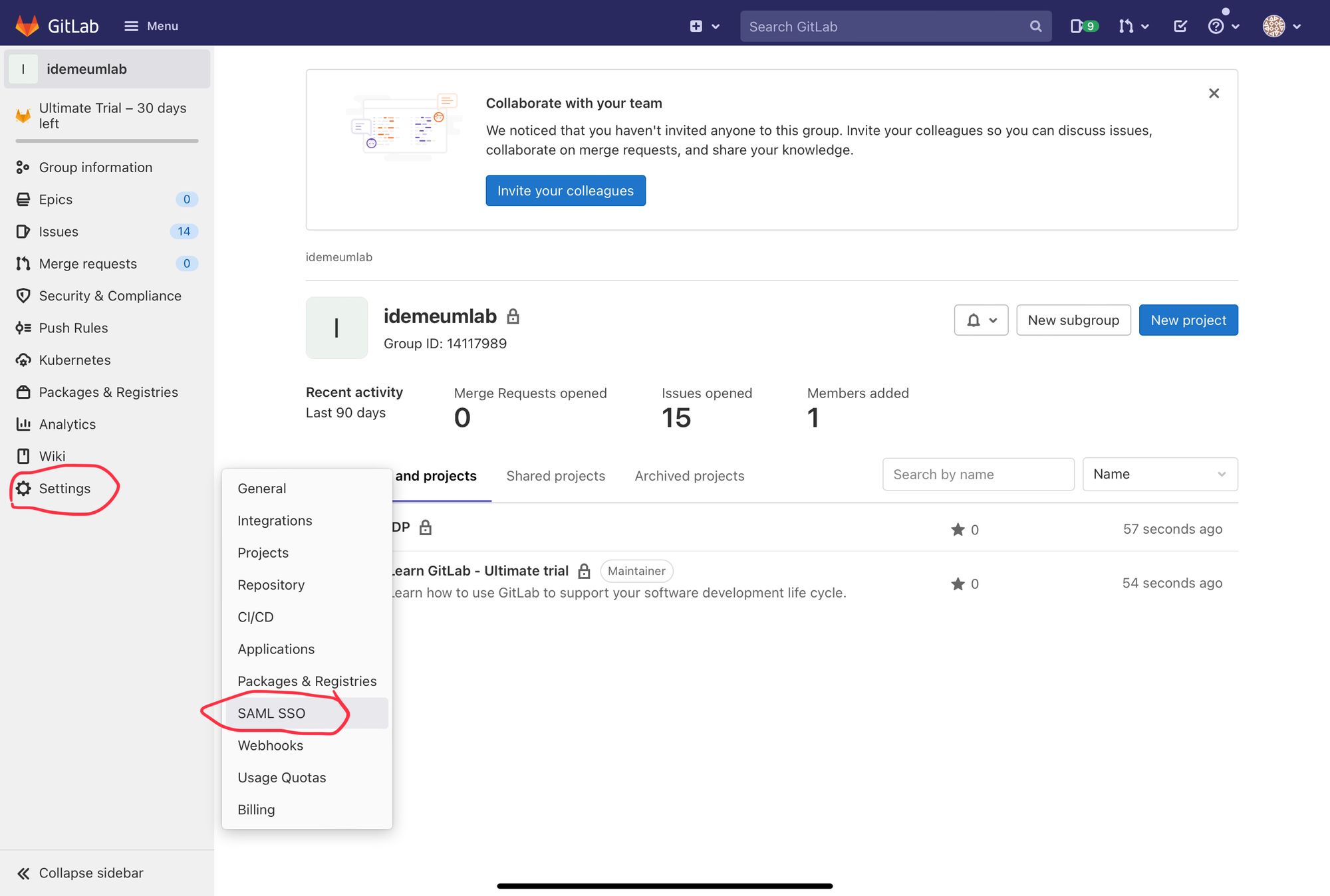
- Navigate to Settings -> SAML SSO
Now you will be using idemeum SAML metadata values obtained in the prerequisites section
- Paste Identity Provider SSO URL and Certificate fingerprint values that you obtained in the previous section
- Choose the default membership role for the users signing in with SAML SSO
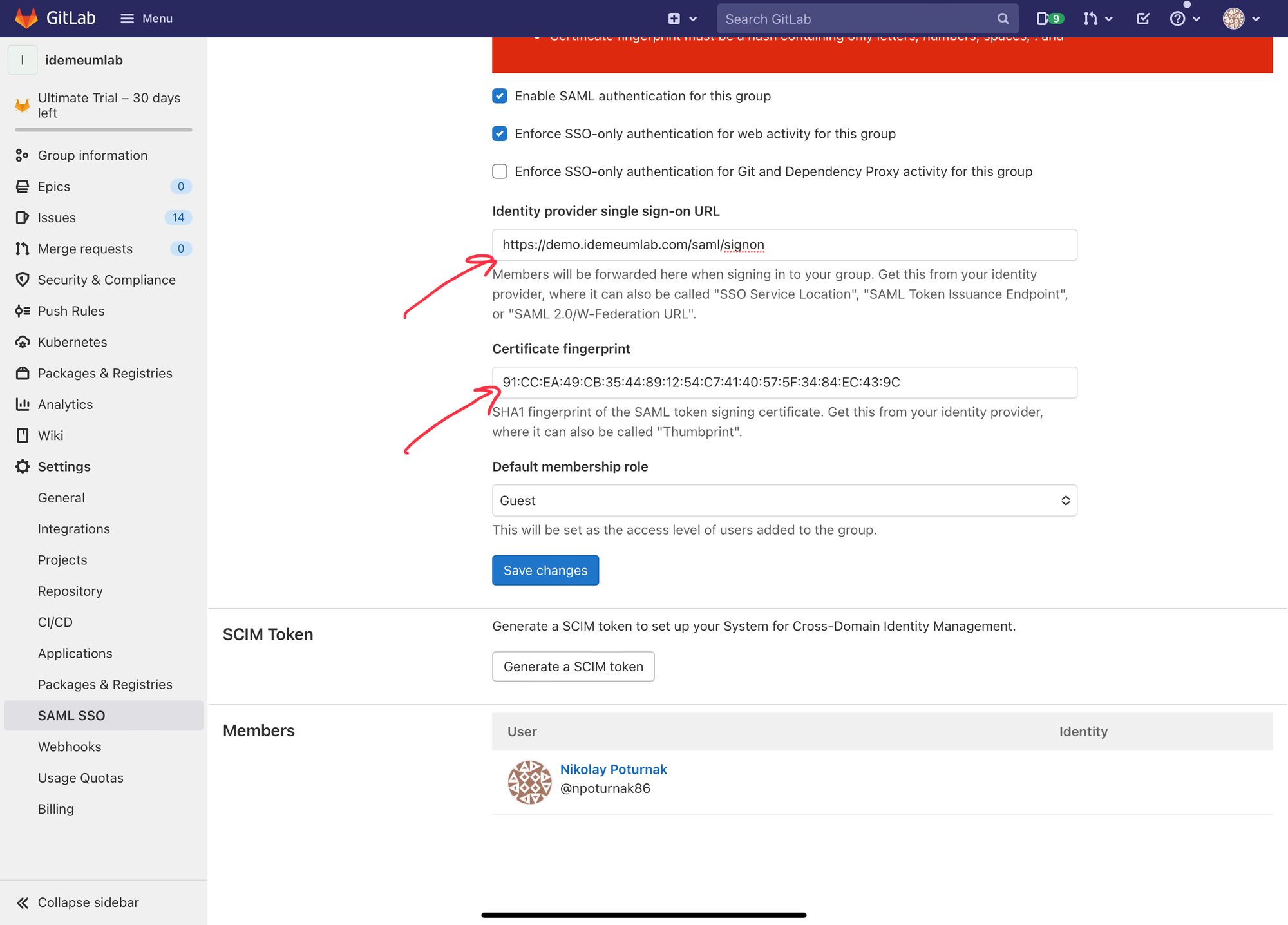
- Click Save changes
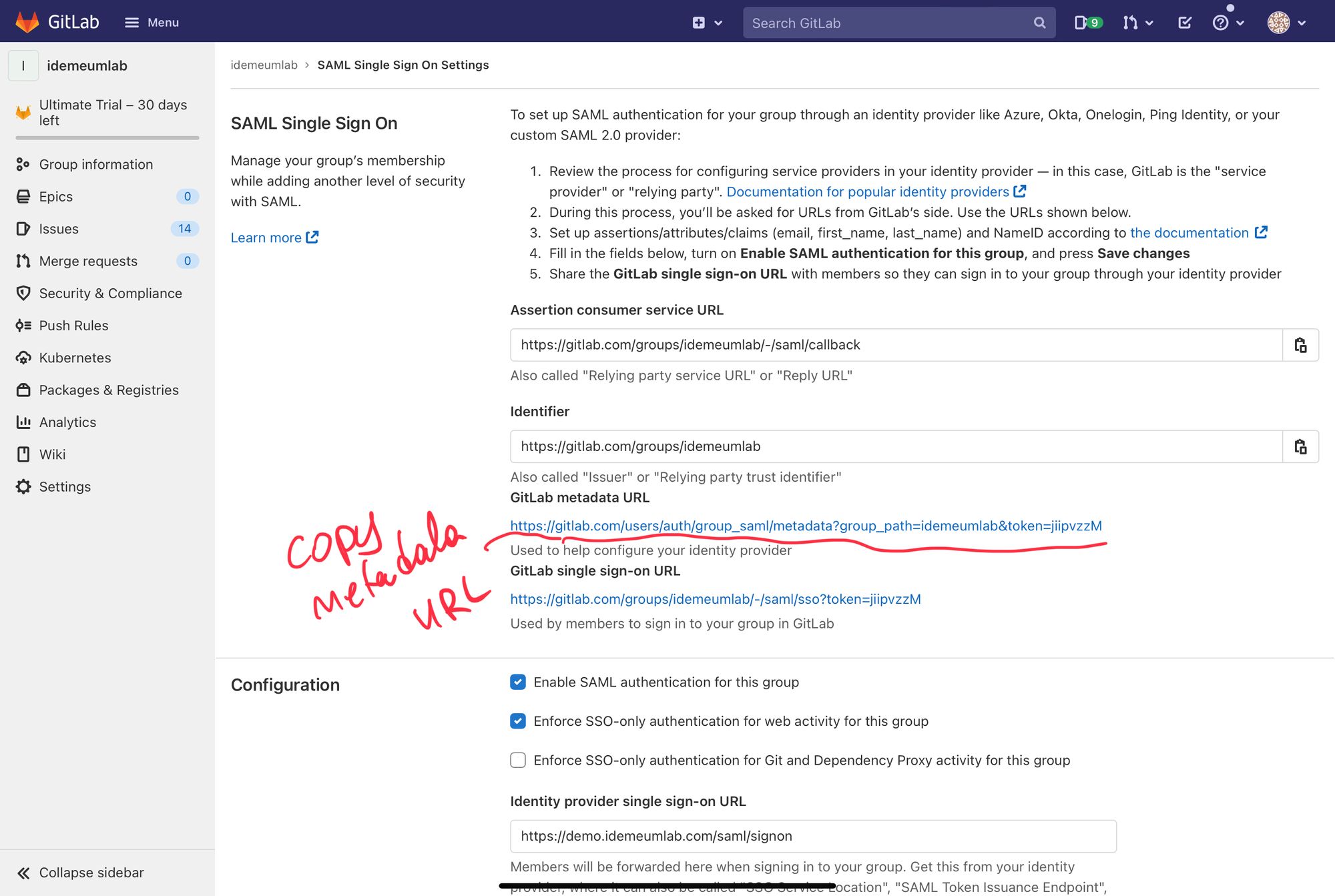
- Now you can grab GitLab metadata URL as you will need that for idemeum SSO configuration
Configure SSO in idemeum
- Navigate to your idemeum admin portal at https://[your domain].idemeum.com/adminportal
- Click Applications in the left menu
- Search for GitLab application and click Add App
- Click SAML at the top navigation menu
- Paste the metadata URL link that you obtained from GitLab and click Load config
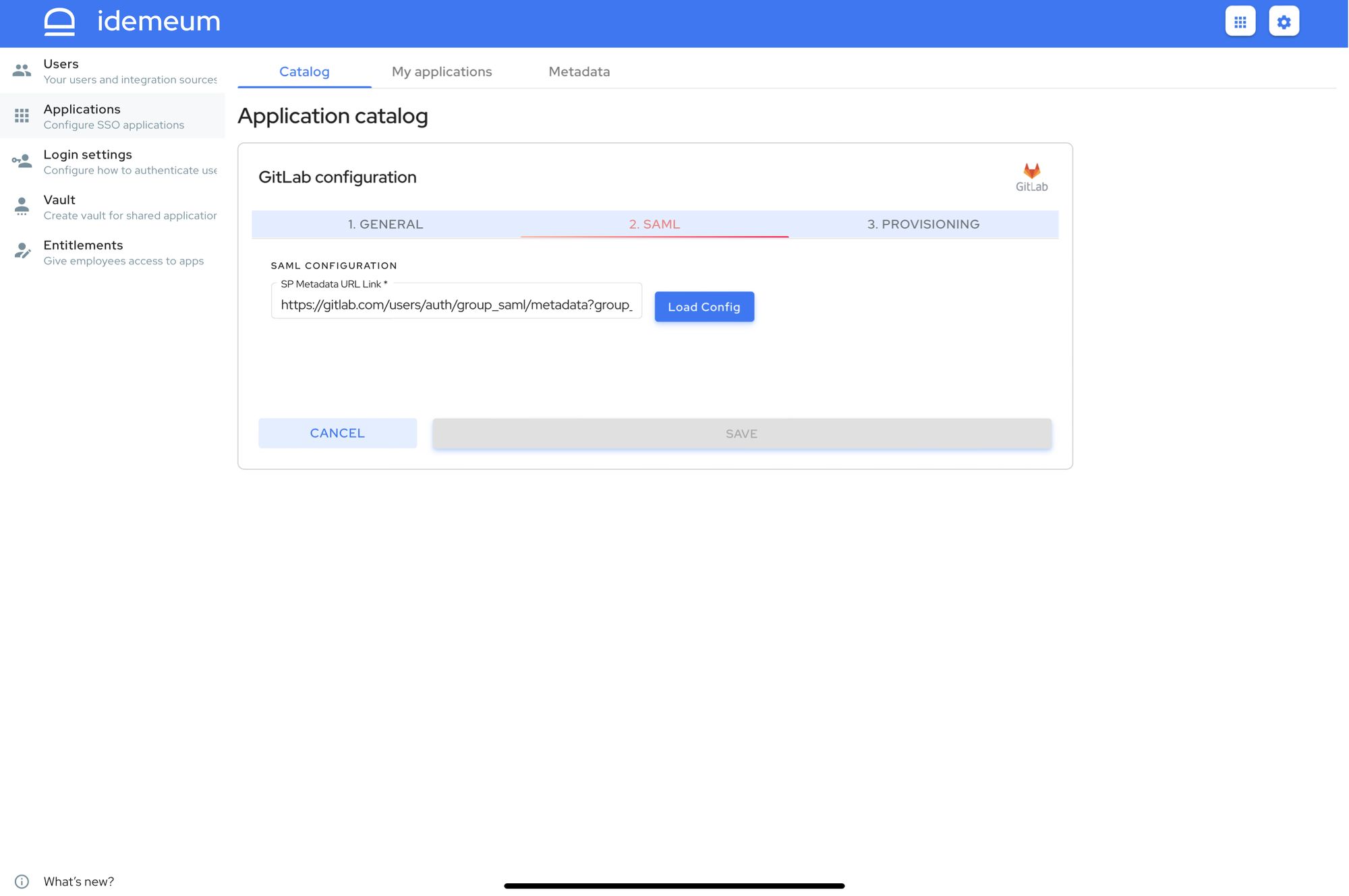
- Click Save
Automated provisioning with SCIM
- Navigate to your Groups in GitLab admin dashboard
- Choose the group you want to enable SSO. Navigate to Settings -> SAML SSO
- Scroll down to SCIM token section
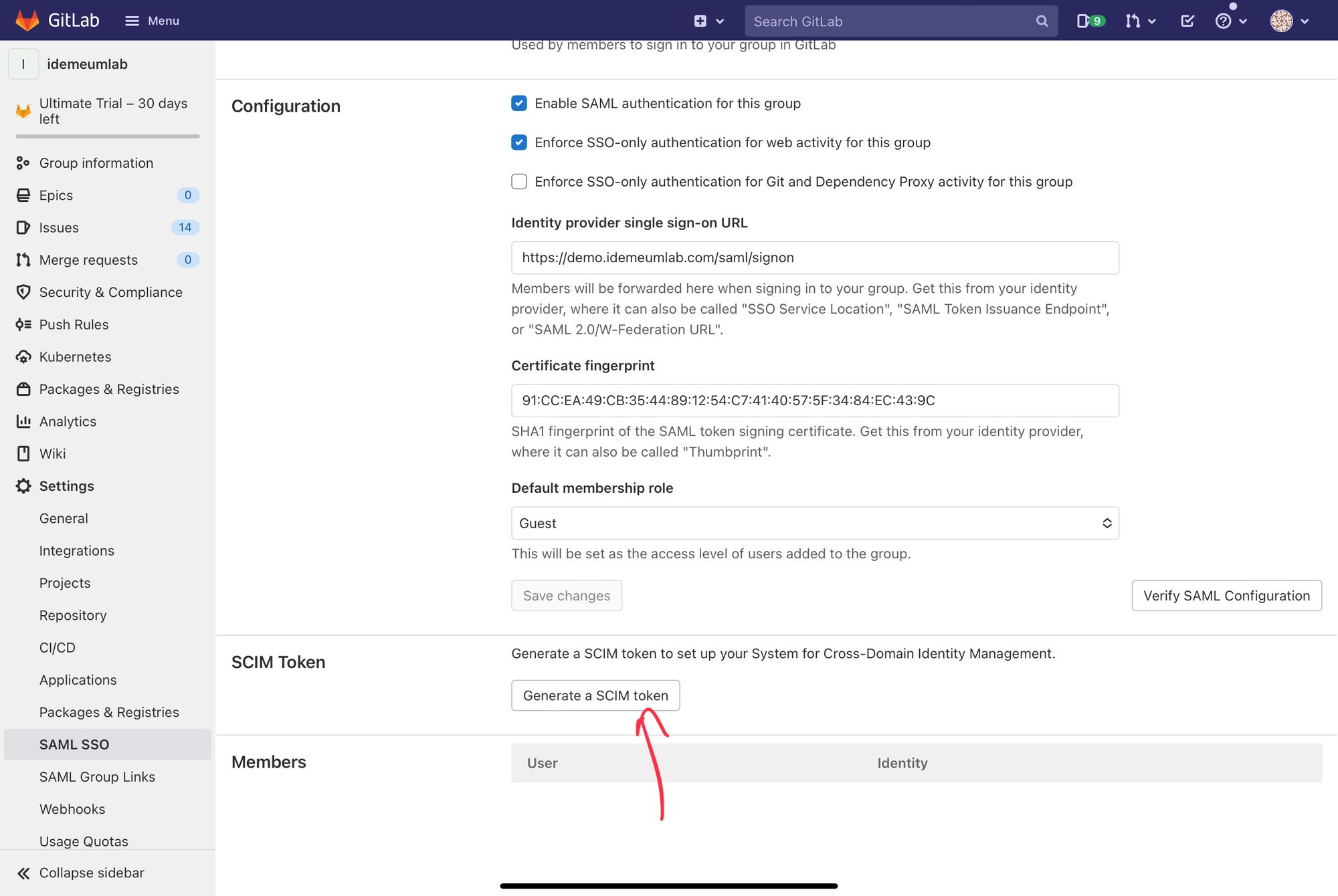
- Click Generate a SCIM token
- From the new window copy Your new SCIM token and SCIM API endpoint URL. You will need these values for idemeum configuration
- Navigate back to idemeum GitLab app configuration
- Click on Provisioning section
- Enter SCIM Base URL and Access Token that you obtained from GitLab
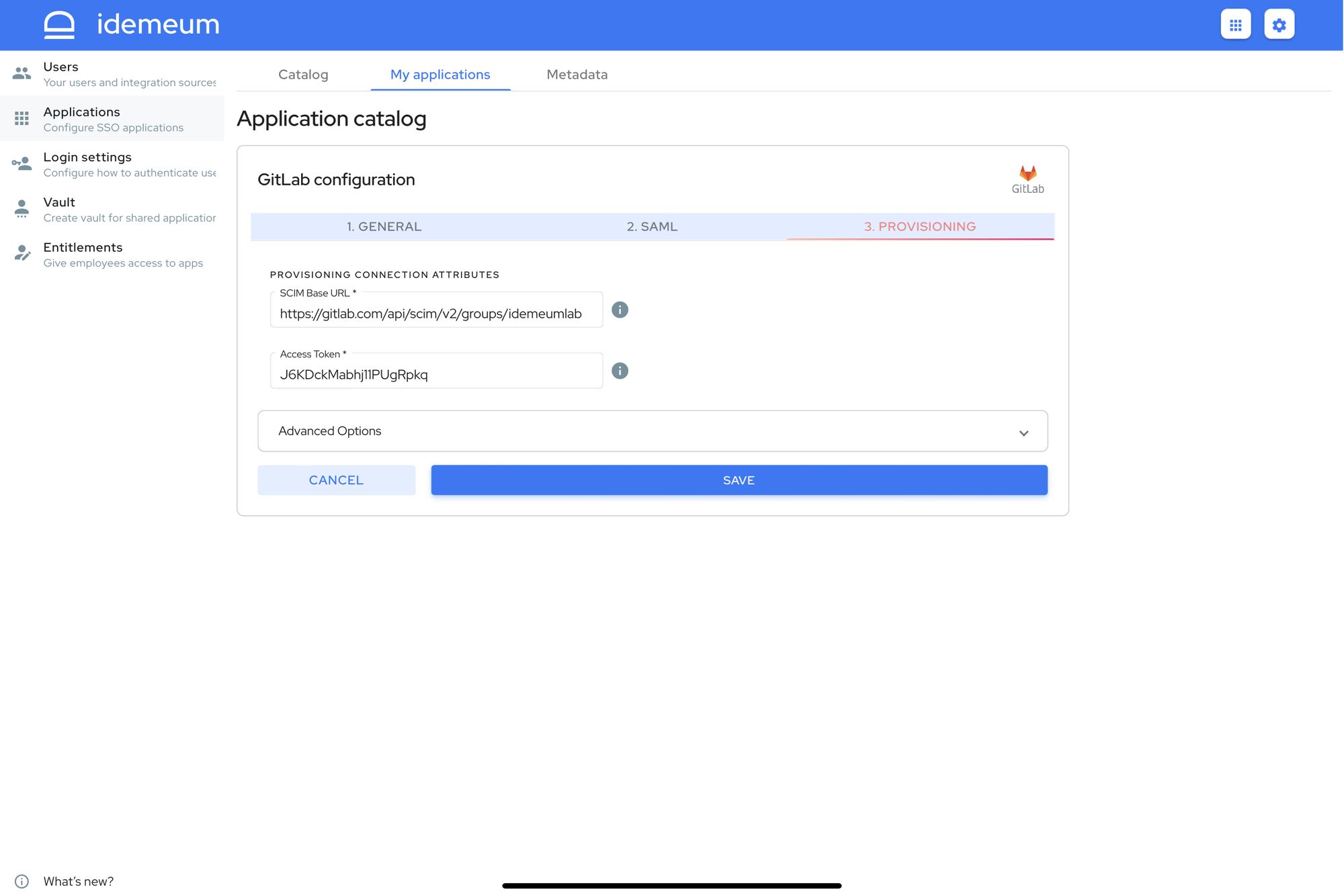
- Click Save
Application entitlements
Before users can access applications you need to make sure you entitle applications to them. In idemeum admin portal navigate to Entitlements section to assign applications to your employees.
SSO login flows
GitLab dashboard supports only IDP Initiated Flow for SSO.
IDP Initiated flow
With this flow users first navigate to idemeum user catalog and then click on GitLab icon to launch application.


