Capabilities overview
GitHub is a software code hosting and collaboration tool with a community of millions of people using it to build software, share information, collaborate on projects, offer support, and more. GitHub also creates and supports development tools like Atom, Electron, and Desktop.
| Supported capability | Required plan | Details |
|---|---|---|
| Passwordless SSO | Enterprise plan | High SSO tax |
| Automated provisioning | Enterprise plan | SCIM 2.0 (create, remove, update accounts) |
| Password manager | Any | Auto-fill / Auto-capture |
Prerequisites
You will need to collect and prepare idemeum SAML metadata parameters:
- Identity Provider SSO URL
- Identity Provider Entity ID
- Public X509 certificate (PEM format)
Instructions for how to obtain your idemeum SAML metadata parameters are below.
Single Sign-On (SAML)
Configure SSO in idemeum
- Navigate to your idemeum admin portal at https://[your domain].idemeum.com/adminportal
- Click Applications in the left menu
- Search for GitHub application and click Add App
- Navigate to SAML configuration
- Enter your GitHub organization name. All other parameters are preconfigured for GitHub. Organization name can be found in your GitHub URL -> https://github.com/orgs/[organization name]/dashboard
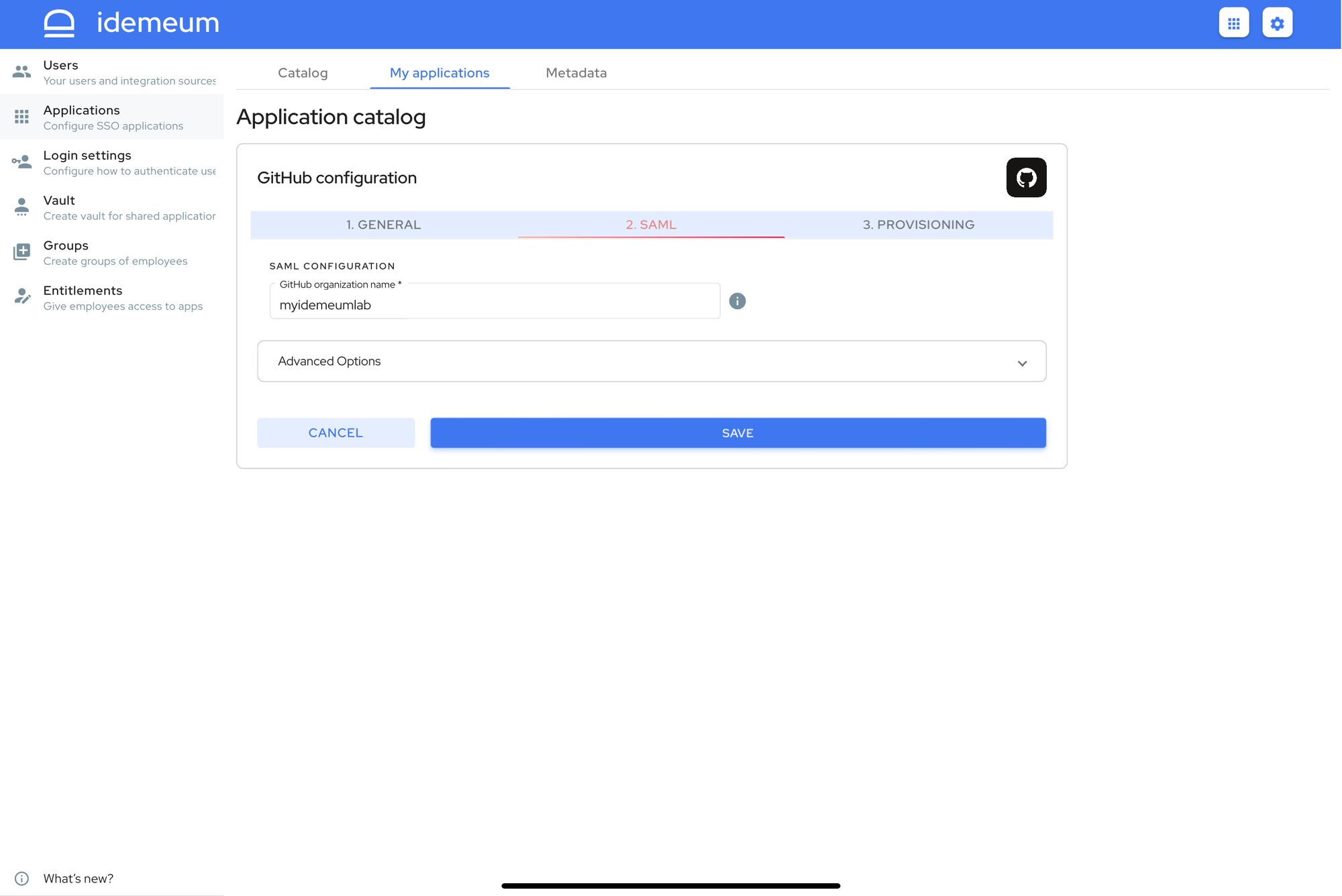
- Click Save
- Proceed to Entitlements on the left menu and entitle GitHub application to yourself. You will need that for testing purposes.
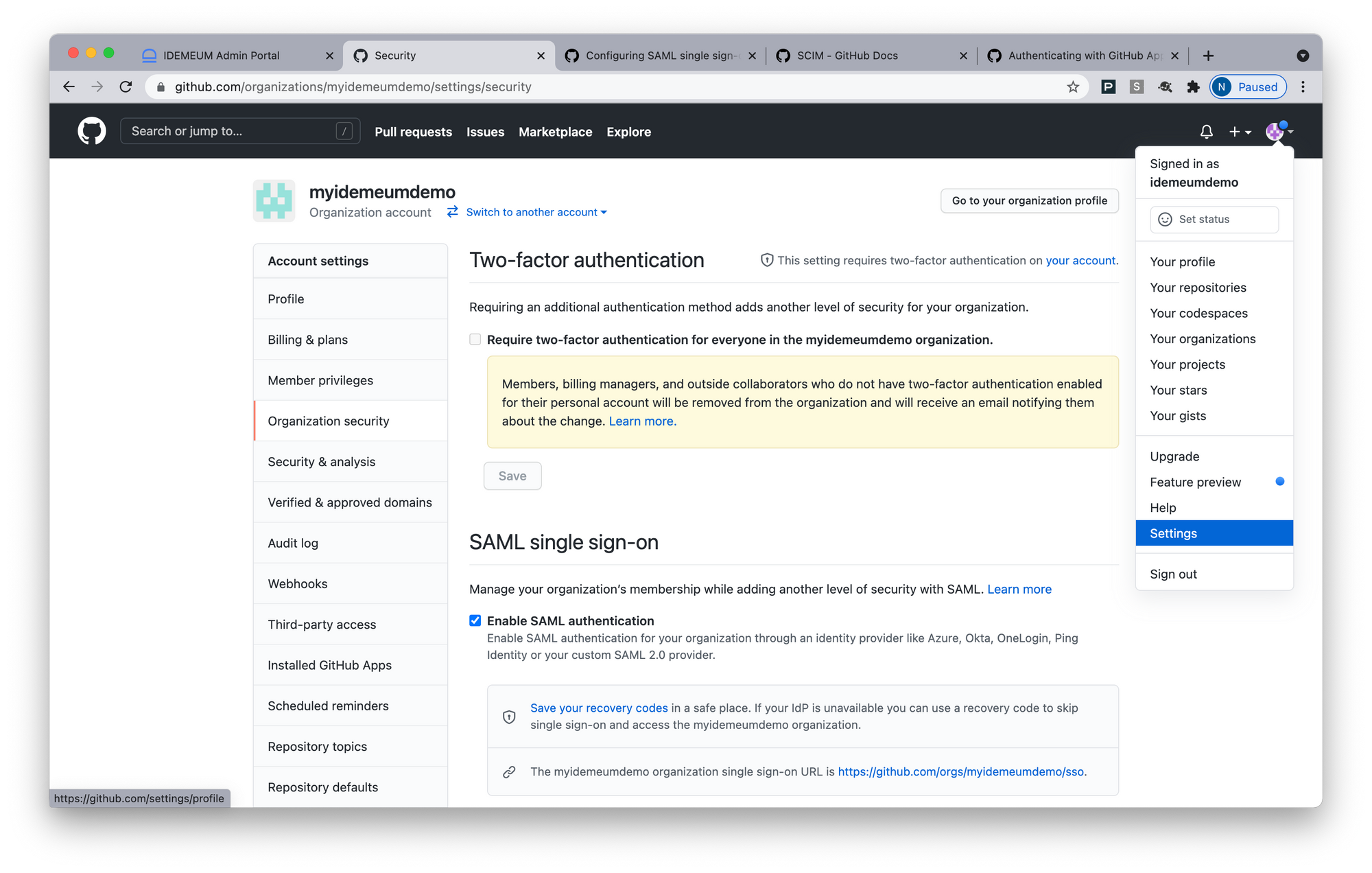
Configure SSO in Github
- Access your GitHub account
- Click Account -> Your organizations
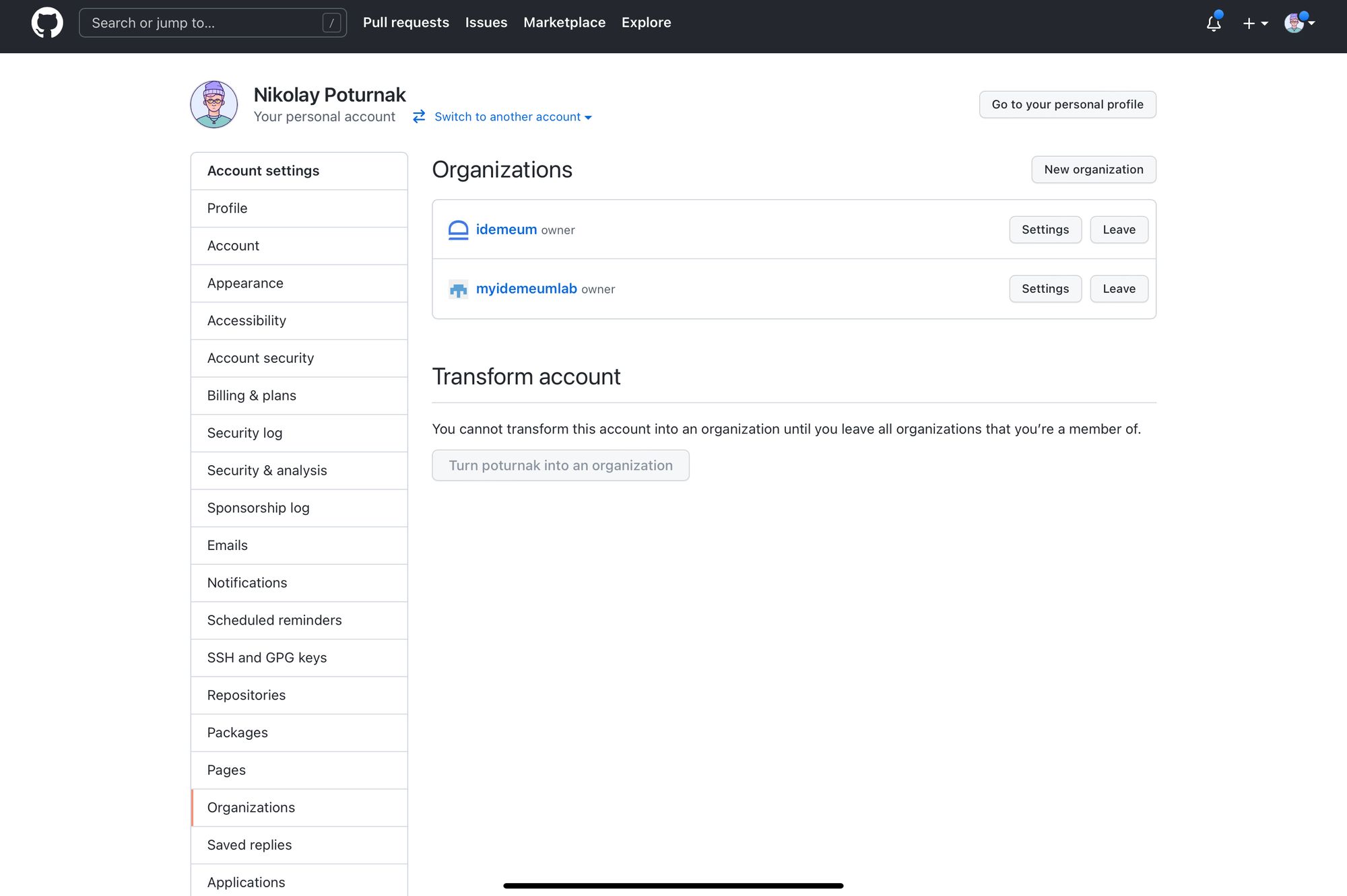
- Choose the organization for which you would like to configure SSO
- Click Settings -> Organization security
- Click Enable SAML authentication
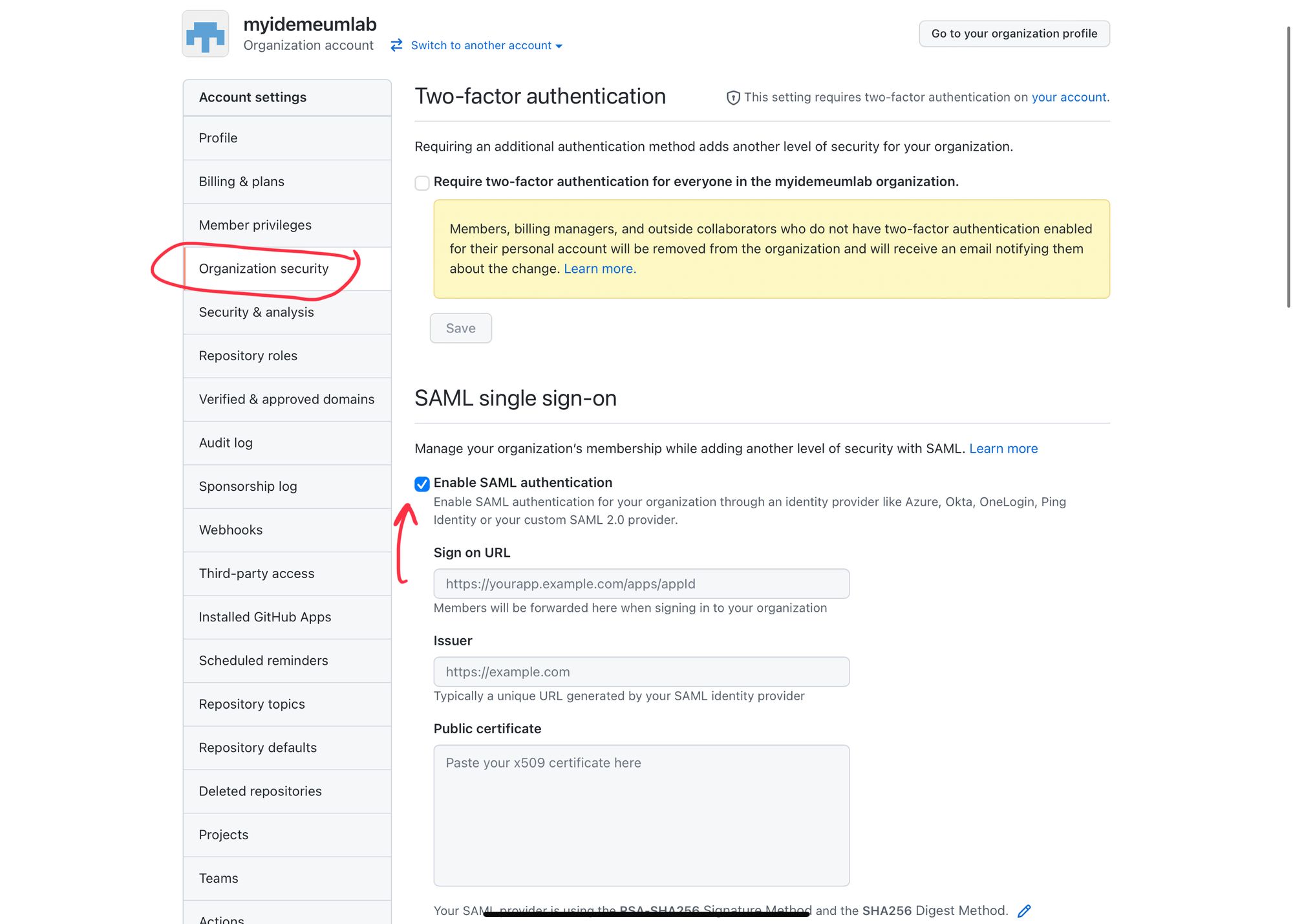
- For Sign on URL enter Identity Provider SSO URL that you obtained in prerequisites section
- For Issuer enter Identity Provider Entity ID that you obtained in prerequisites section
- For Public certificate enter Public X509 certificate (PEM format) that you obtained from prerequisites section
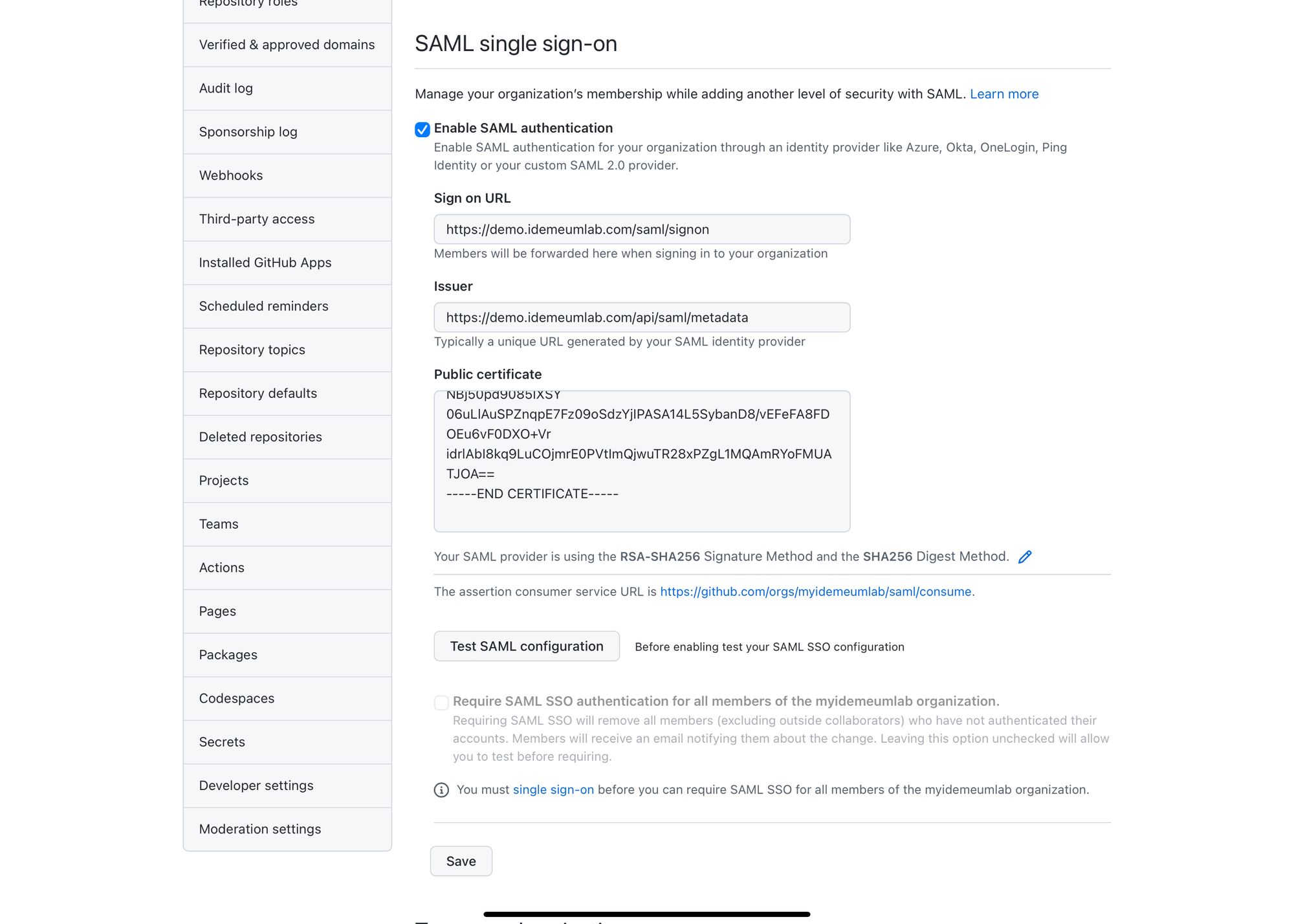
- Make sure you choose SHA256 for Signature and Digest
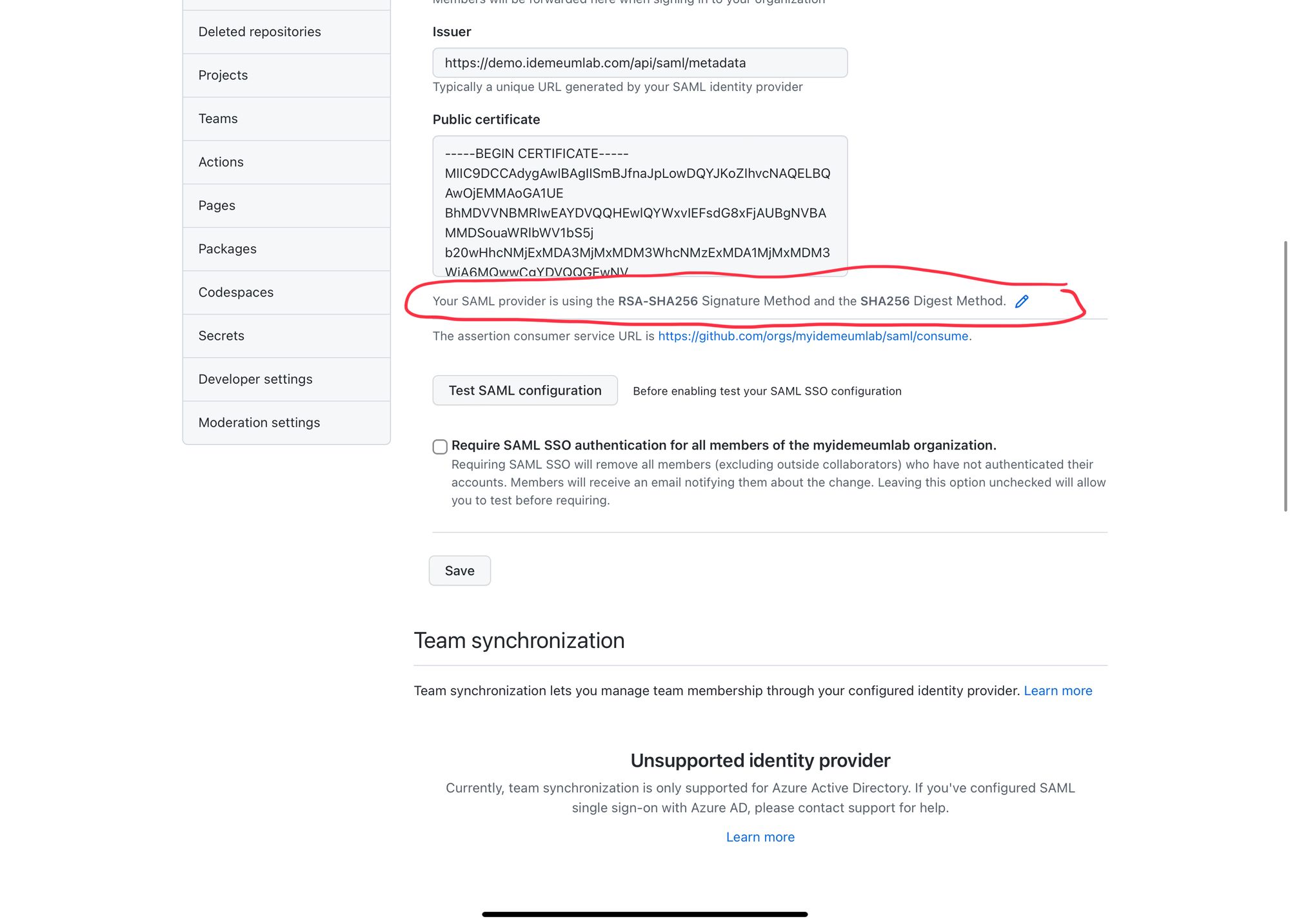
- Click Test SAML configuration. You will be redirected to idemeum and you will need to login with passwordless MFA.
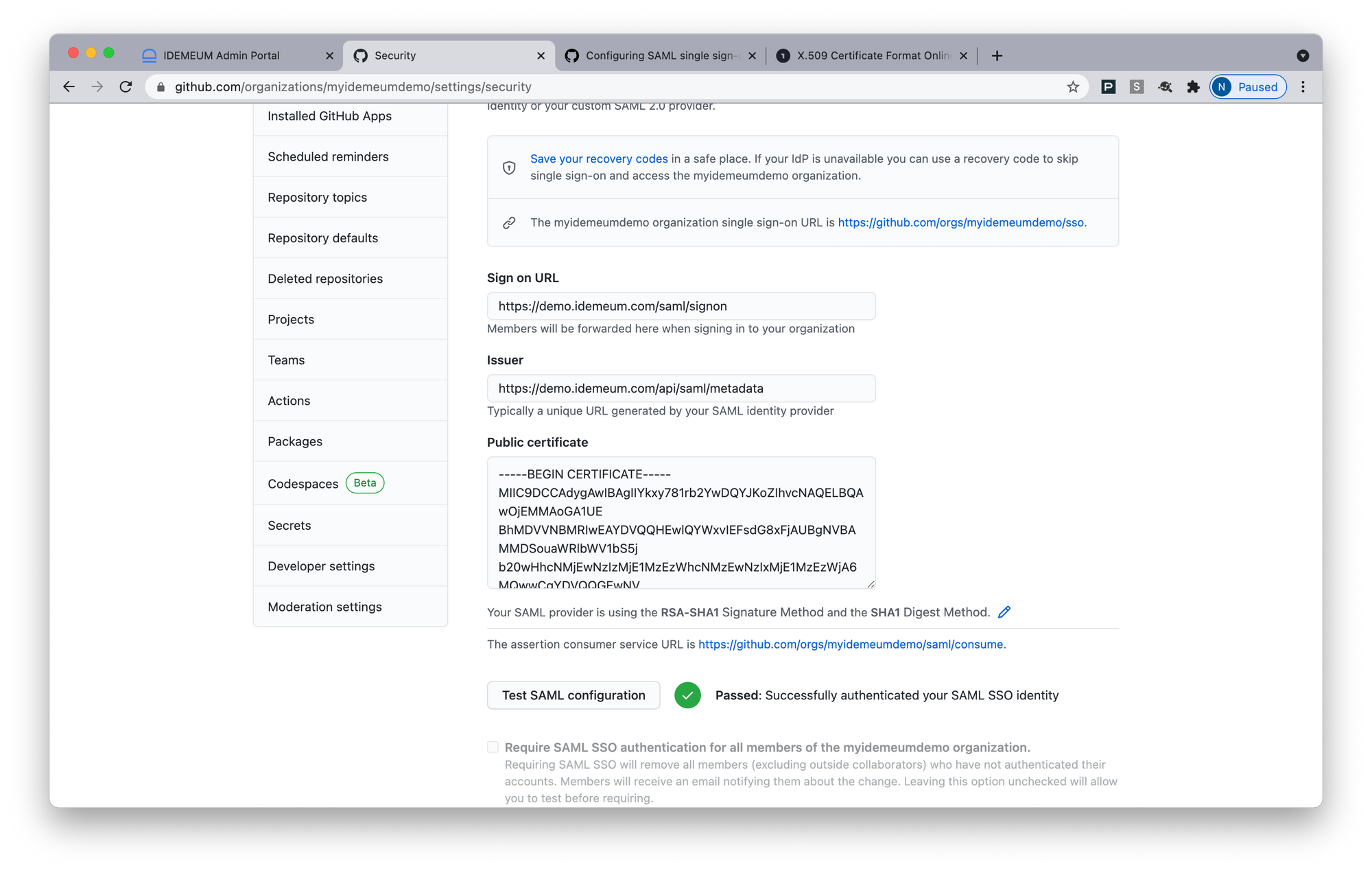
- Click Save at the bottom of the page if the test is passed
- Make sure you save Recovery Codes to make sure you have access to your account in case SAML SSO in not available
- If everything works great you can enable SSO for all users in your organization by clicking Require SAML SSO authentication for all members
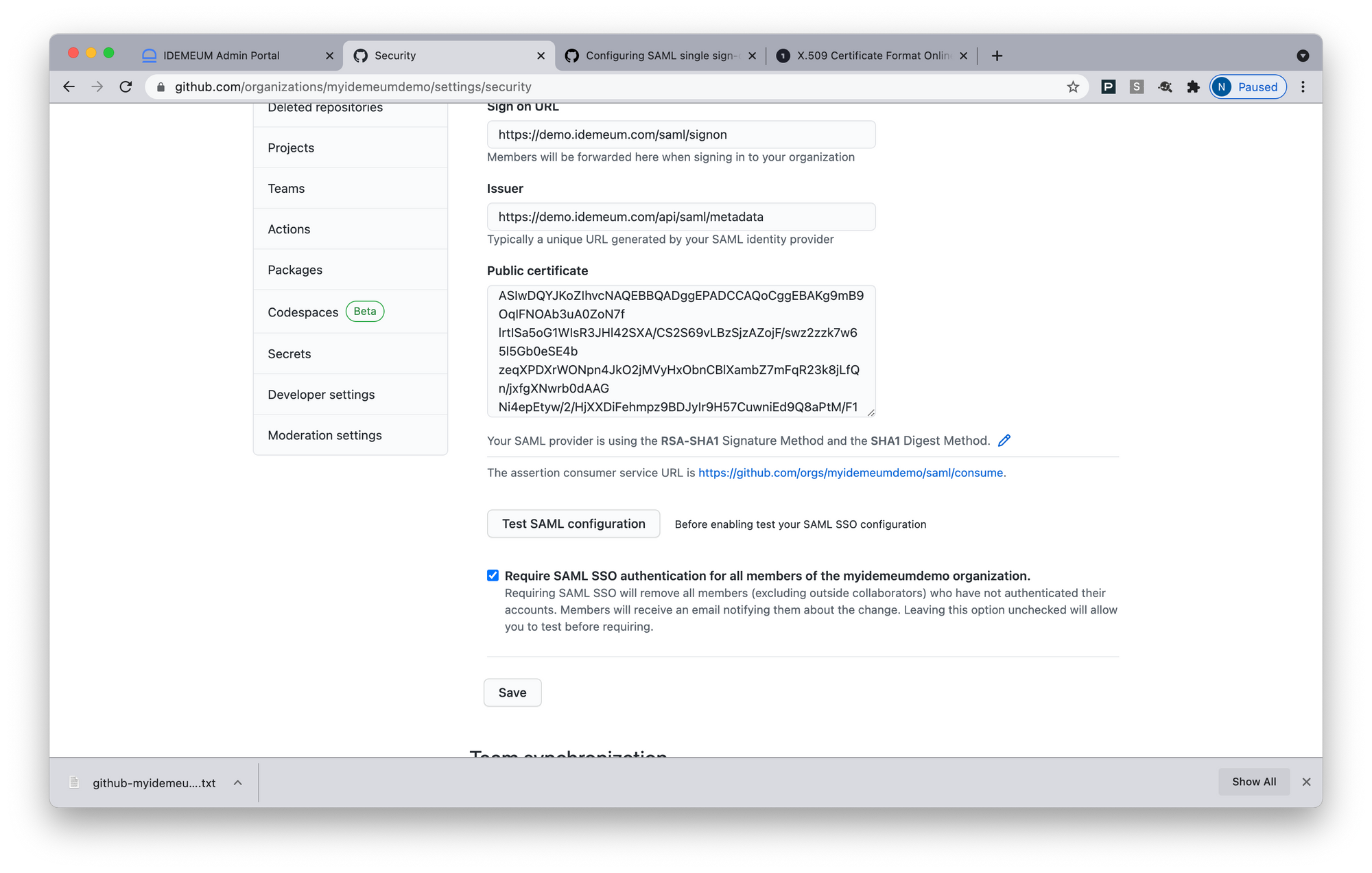
- Click Save
Automated provisioning with SCIM
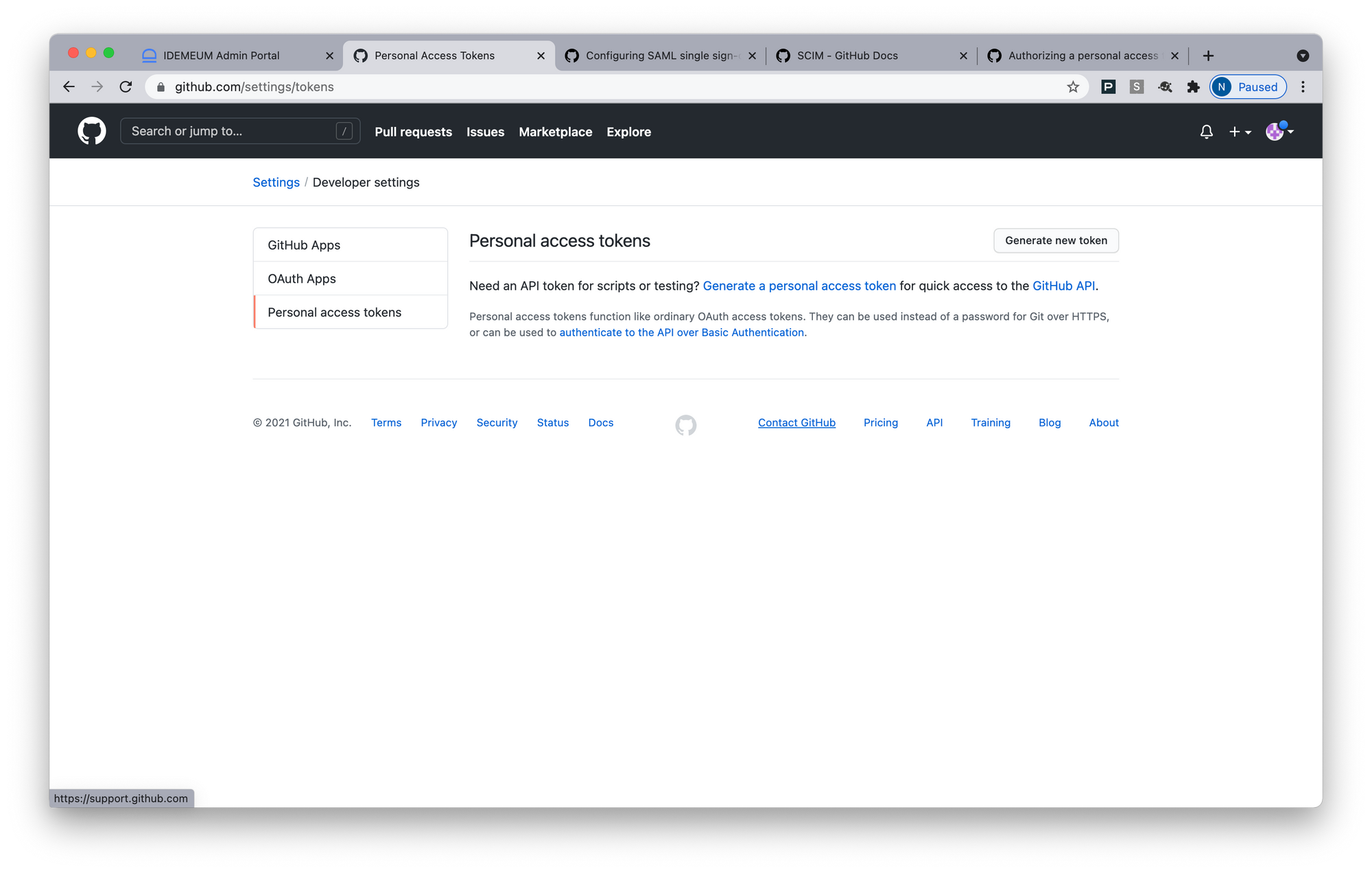
- Click on the icon at the top right corner of the screen and access Settings
- In the left menu click Developer Settings
- Choose Personal access tokens
- Now you will create an access token. Choose the expiration time and give the token the following scopes: admin:org and user.
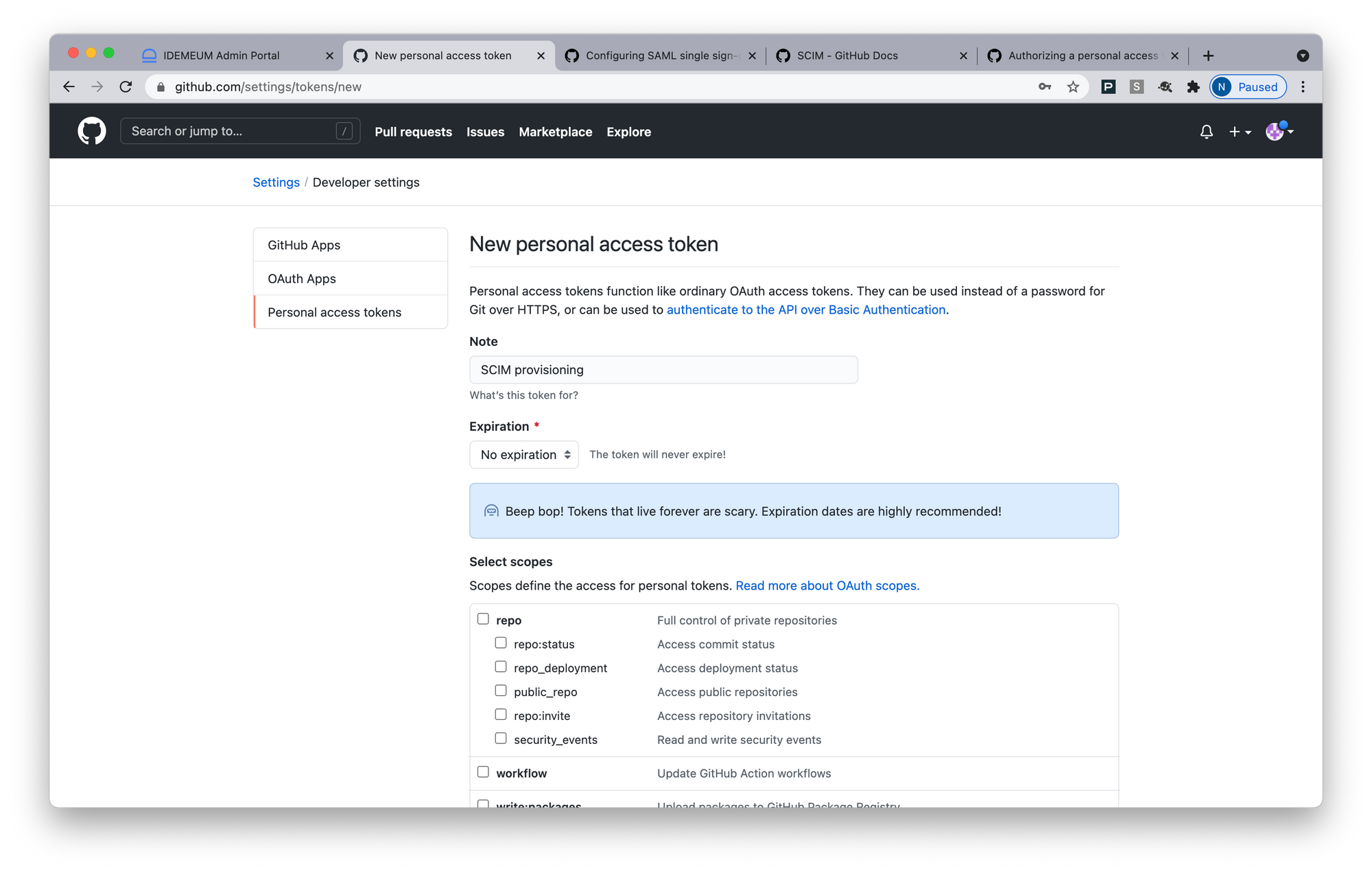
- Make sure you copy token after you generate it. You will need the token for your idemeum configuration.
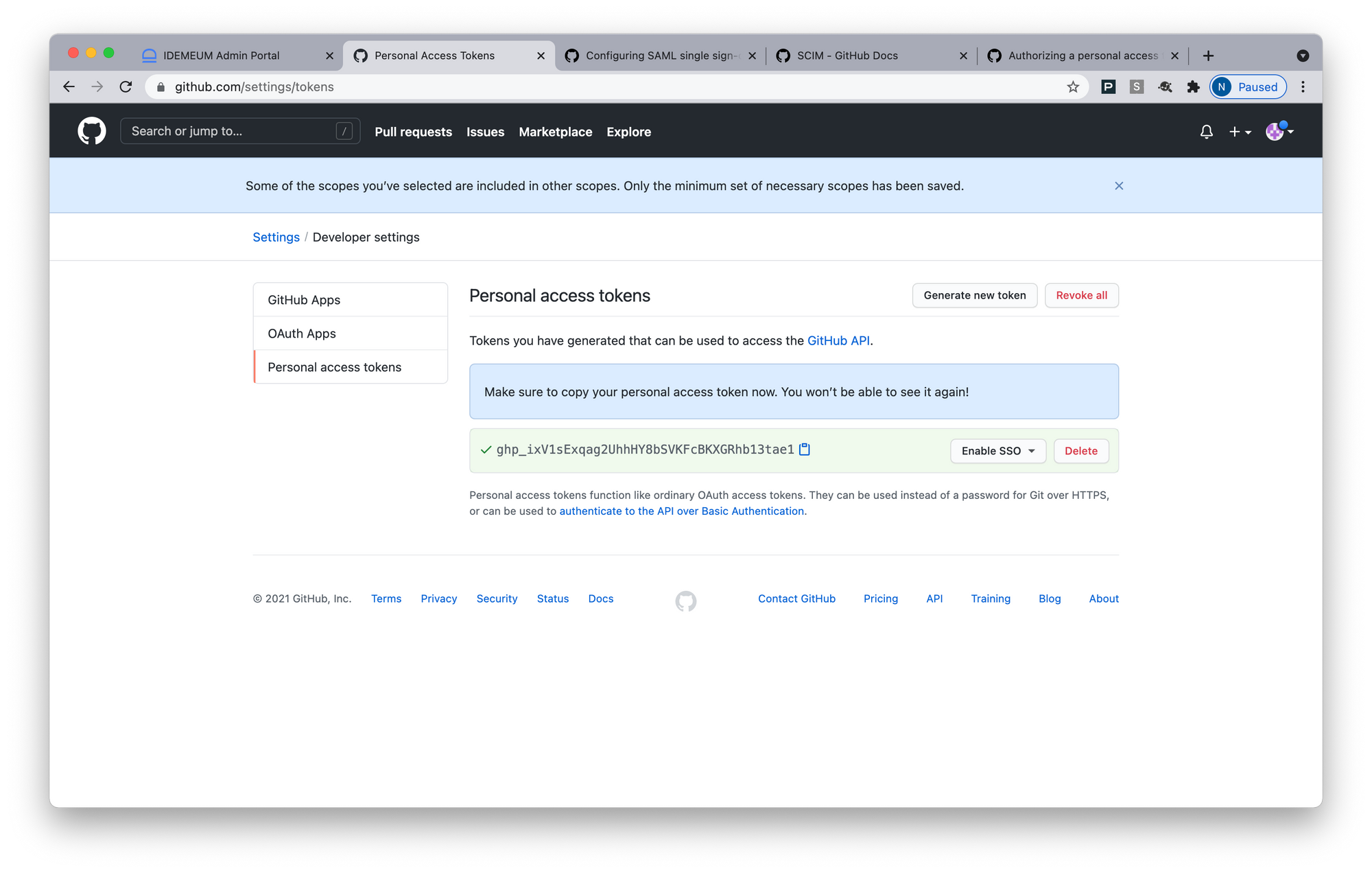
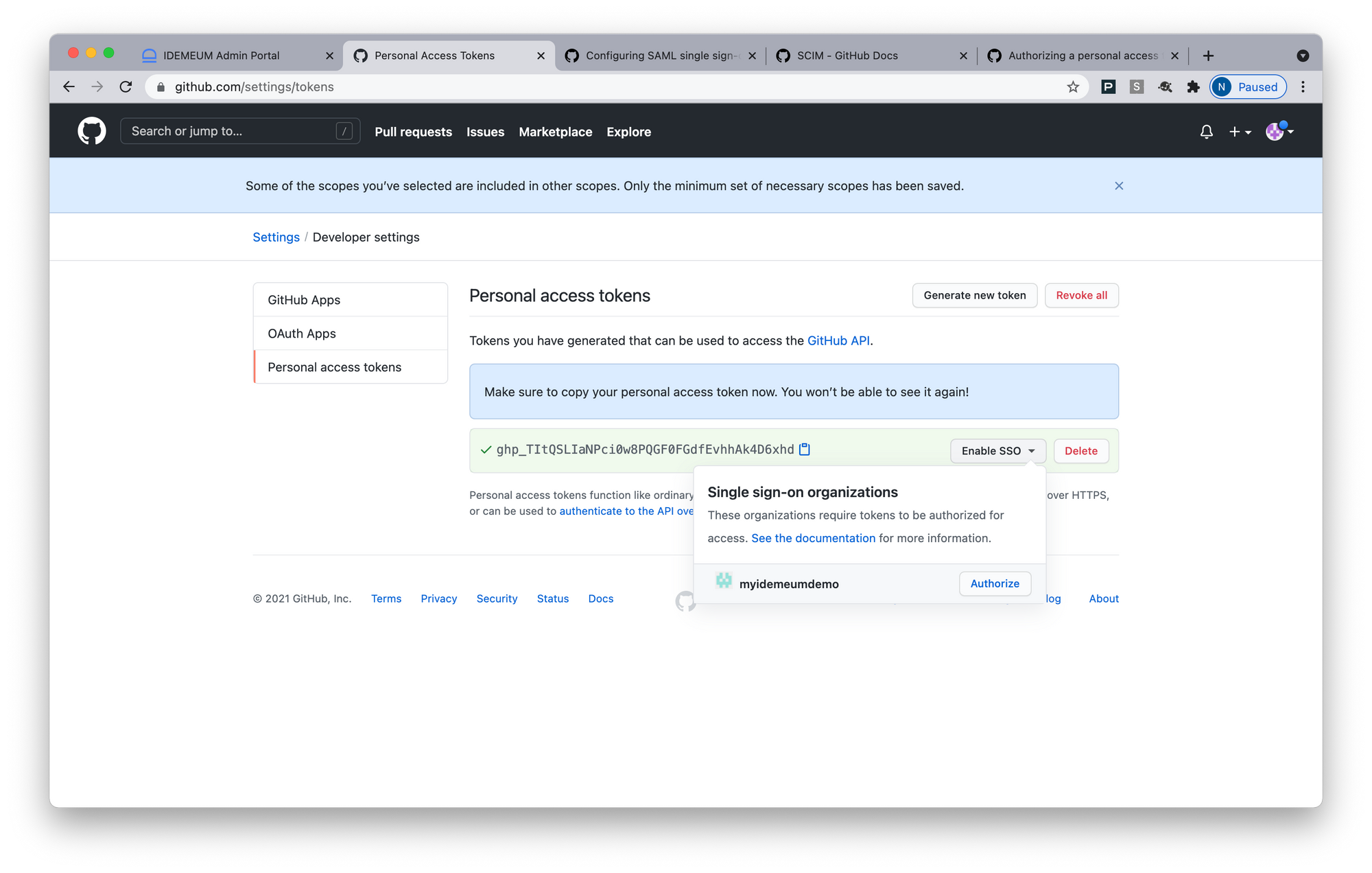
- Now Authorize this token to be used with SSO. Click Single Sign-On and then choose Authorize.
- Access Provisioning section for your GitHub app in idemeum
- Enter your GitHub organization name. Organization name can be found in your GitHub URL -> https://github.com/orgs/[organization name]/dashboard
- For Access Token enter the GitHub token you just created
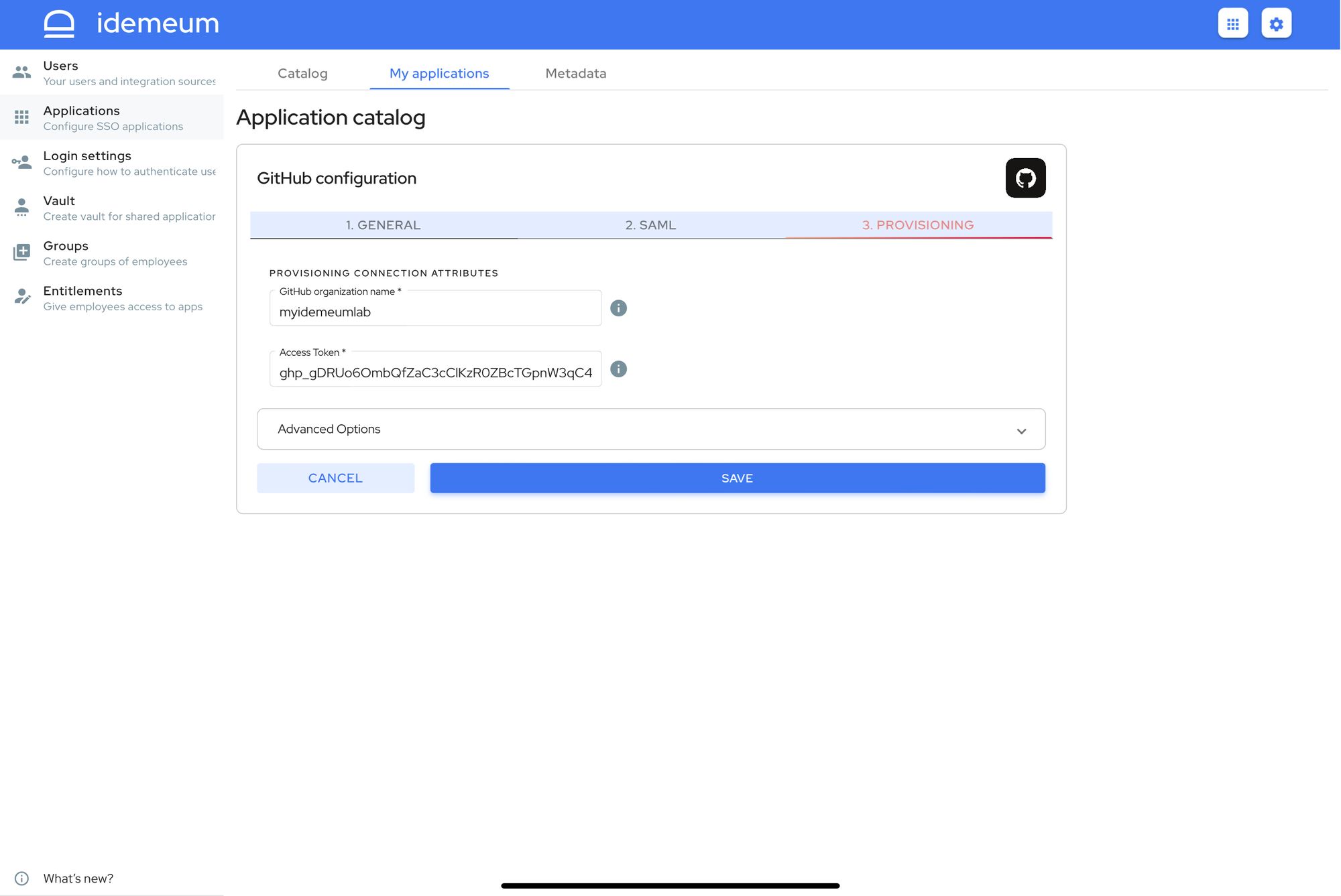
- You can now save configuration and test provisioning
Application entitlements
Before users can access applications you need to make sure you entitle applications to them. In idemeum admin portal navigate to Entitlements section to assign applications to your employees.
SAML SSO login flows
GitHub supports both:
- IDP Initiated Flow
- SP Initiated Flow
IDP Initiated flow
With this flow users first navigate to idemeum user catalog and then click on GitHub icon to launch application.
SP Initiated flow
With this flow users can directly go to GitHub and login with passwordless SSO.
- Navigate to https://github.com/orgs/[your org name]/sso
- Login with idemeum


