Integration summary
Use this integration guide when your primary Identity Provider is Azure Active Directory and you want to protect everything your employees access with idemeum Passwordless MFA.
You will still manage your users in Azure AD, you will federate your applications with Azure AD, but employees will login with Passwordless MFA into Azure AD portal. If you want idemeum to become your primary Identity Provider, please user Office 365 integration guide instead.
Capabilities overview
Today we support various integrations with Azure AD and Office 365. Please choose the guide that is relevant to your scenario.
| Deployment scenario | Description | Guide |
|---|---|---|
| Hybrid Azure AD | Passwordless MFA for AAD + AD | Guide |
| Cloud Azure AD | Passwordless MFA for Azure AD | Guide |
| Office 365 | Passwordless SSO for Office 365 | Guide |
Deployment scenarios
Hybrid Azure AD
Hybrid Azure AD is the deployment where customers leverage both Azure AD in the cloud as well as Active directory on-premises.
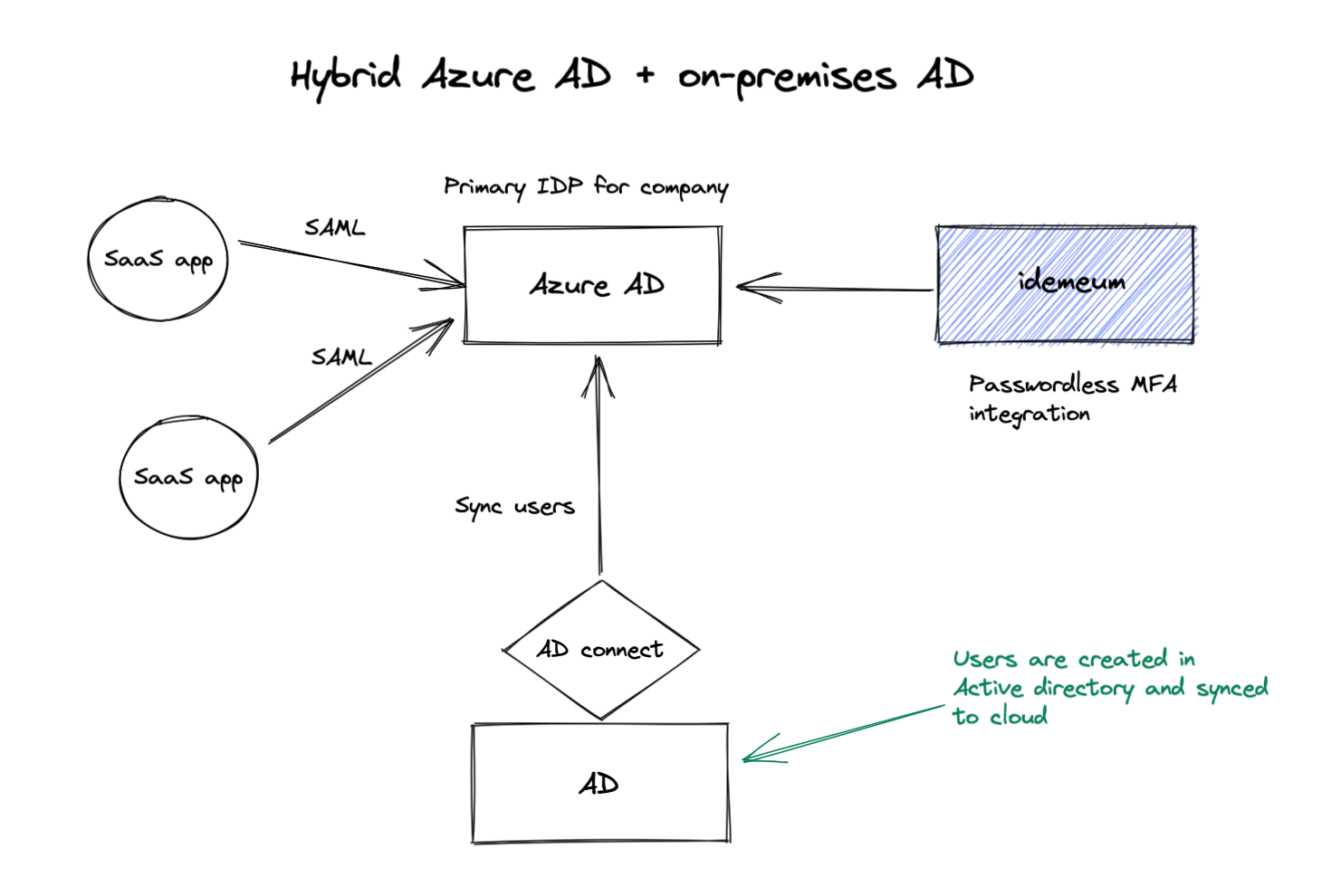
- Role of idemeum - In this integration scenario Azure AD is the primary Identity Provider for an organization, and idemeum provides Passwordless MFA login to all company resources.
- Source of users - source of users is Active Directory on-premises. idemeum is connecting to Azure AD using oAuth in order to read data for passwordless employee onboarding. It is assumed that Azure AD has personal email or phone number attributes for passwordless employee onboarding.
- User creation - users are created in Active directory on-premises. Then these users are pushed to Azure AD using AD connect and later can be used by idemeum for employee onboarding.
- ImmutableID - Azure AD uses the ImmutableID attribute to uniquely identify users. For this scenario the ImmutableID is set by active directory and idemeum will sync it to make SAML authentication possible. If for whatever reason ImmutableID is missing, idemeum will set the value to user DID.
- User offboarding - users are off-boarded in Active Directory. We support the the case when users are disabled. Once the user is disabled, the information will propagate to Azure AD, and in turn idemeum will off-board the user from passwordless access. By default we check Azure AD for off-boarded users every 4 hours.
Cloud only Azure AD
Cloud only Azure AD is the deployment where customers only leverage Azure AD in the cloud as primary identity provider.
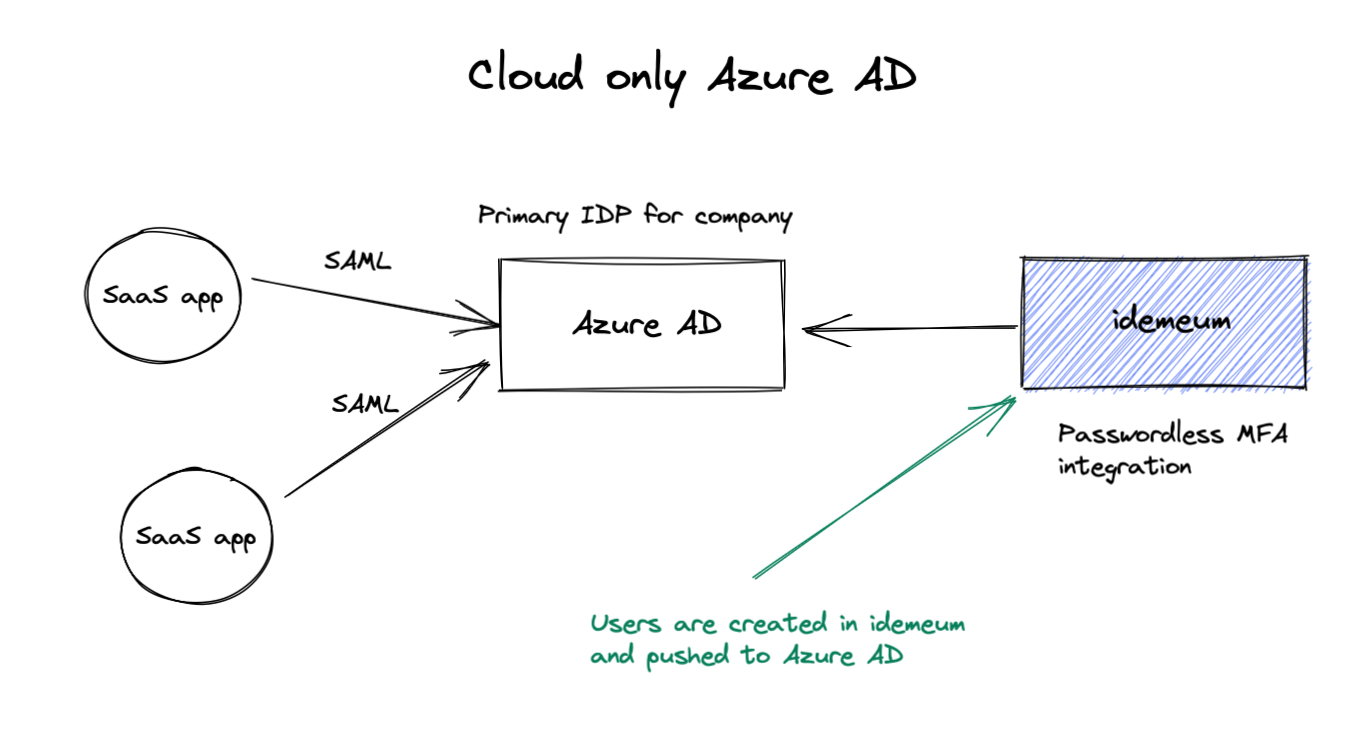
- Role of idemeum - In this integration scenario Azure AD is the primary Identity Provider for an organization, and idemeum provides Passwordless MFA login to all company resources.
- Source of users - source of users is Azure AD. idemeum is connecting using oAuth in order to read data for passwordless employee onboarding. It is assumed that Azure AD has personal email or phone number attributes for passwordless employee onboarding.
- User creation - users are created idemeum directly and are synced to Azure AD. We offer the UI to create users and push them to Azure AD.
- ImmutableID - Azure AD uses the ImmutableID attribute to uniquely identify users. For this scenario the ImmutableID is set by active directory and idemeum will sync it to make SAML authentication possible. If for whatever reason ImmutableID is missing, idemeum will set the value to user DID.
- User offboarding - users are off-boarded directly in idemeum. You can navigate to user management in idemeum and disable / off-board user. Once disabled, user will not be able to access any company resources.
Integration set up
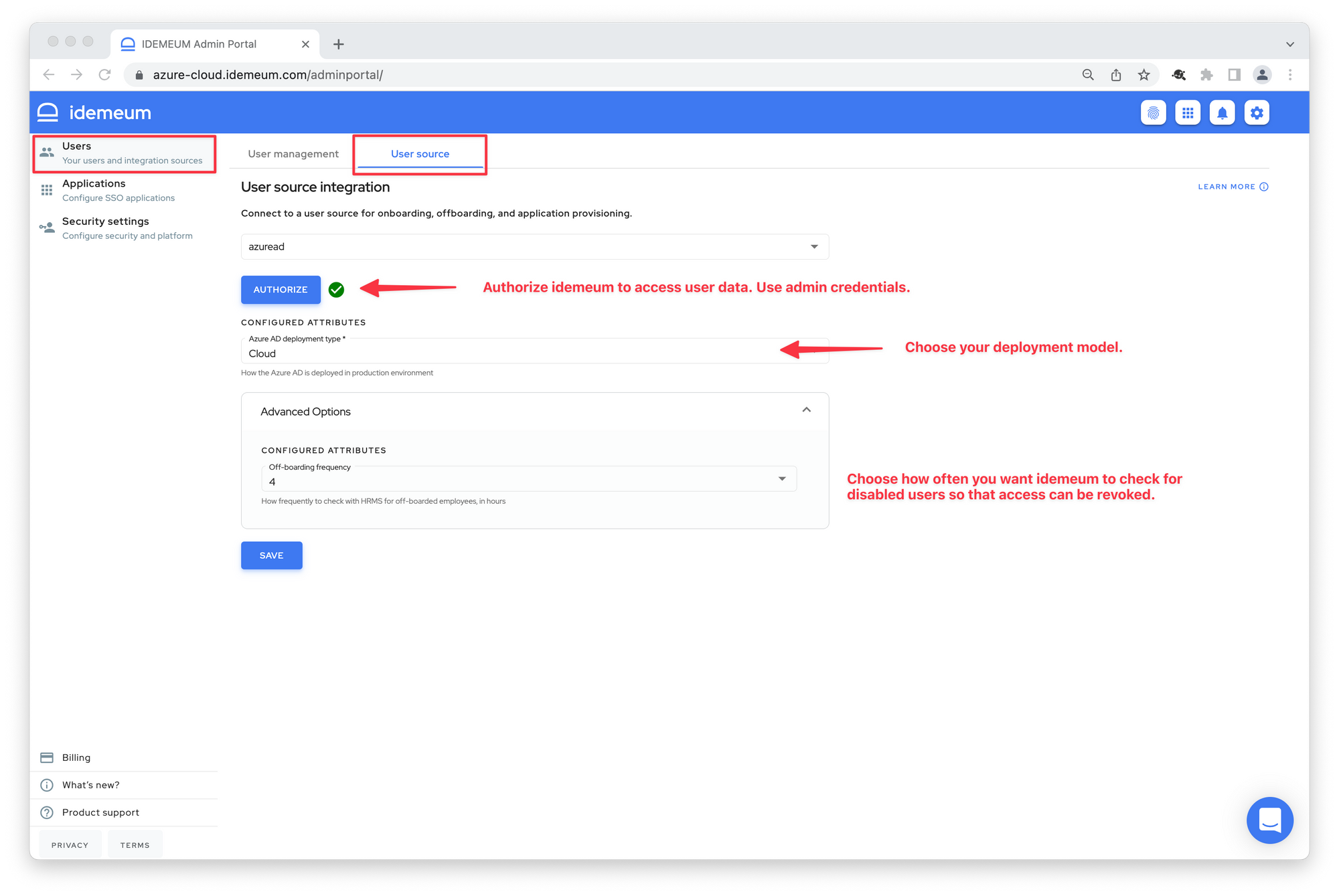
Configuring user source
As a first step we need to set up connection between idemeum and Azure AD so that users can be onboarded into passwordless access.
- Access your idemeum admin portal
- Navigate to Users -> User source
- Choose Azure AD
- Click Authorize and give idemeum access to user data in your Azure AD tenant. We recommend using super admin credentials from onmicrosoft domain when providing access.
- Choose Hybrid or Cloud Azure deployment
- Upon successful connection you will see green checkbox next to Authorize button.
- Optionally you can expand the advanced settings and configure how often you want idemeum to check for disabled users so that we can block access in idemeum when employees are off-boarded.
User onboarding
You can configure what personal claims you want your employees to use when onboarding into idemeum.
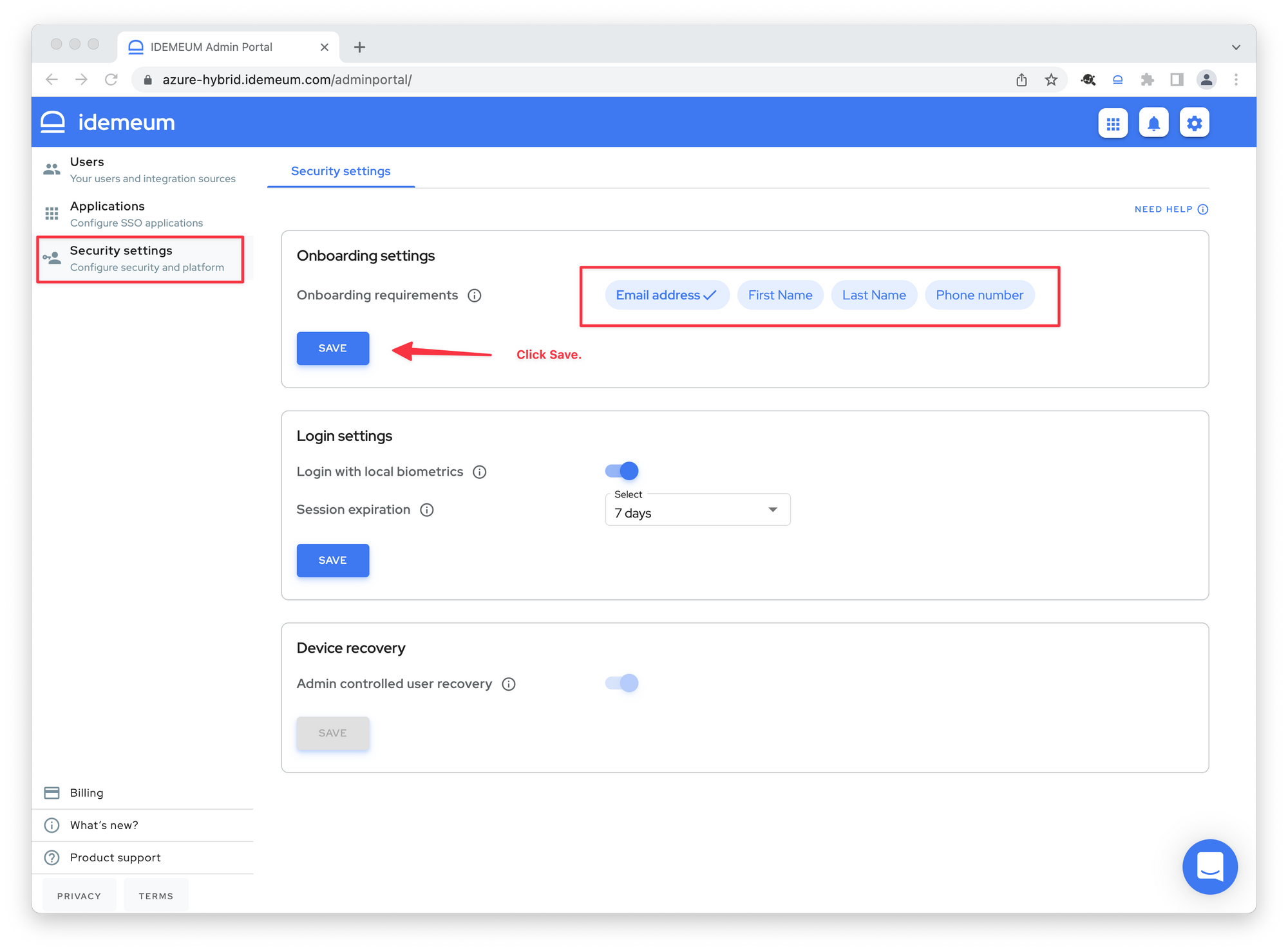
- Navigate to Security settings
- In the onboarding setting choose email, phone, or first-name / last-name to onboard your users into idemeum passwordless access.
Configuring SAML federation
- Navigate to Applications and search for Azure AD application
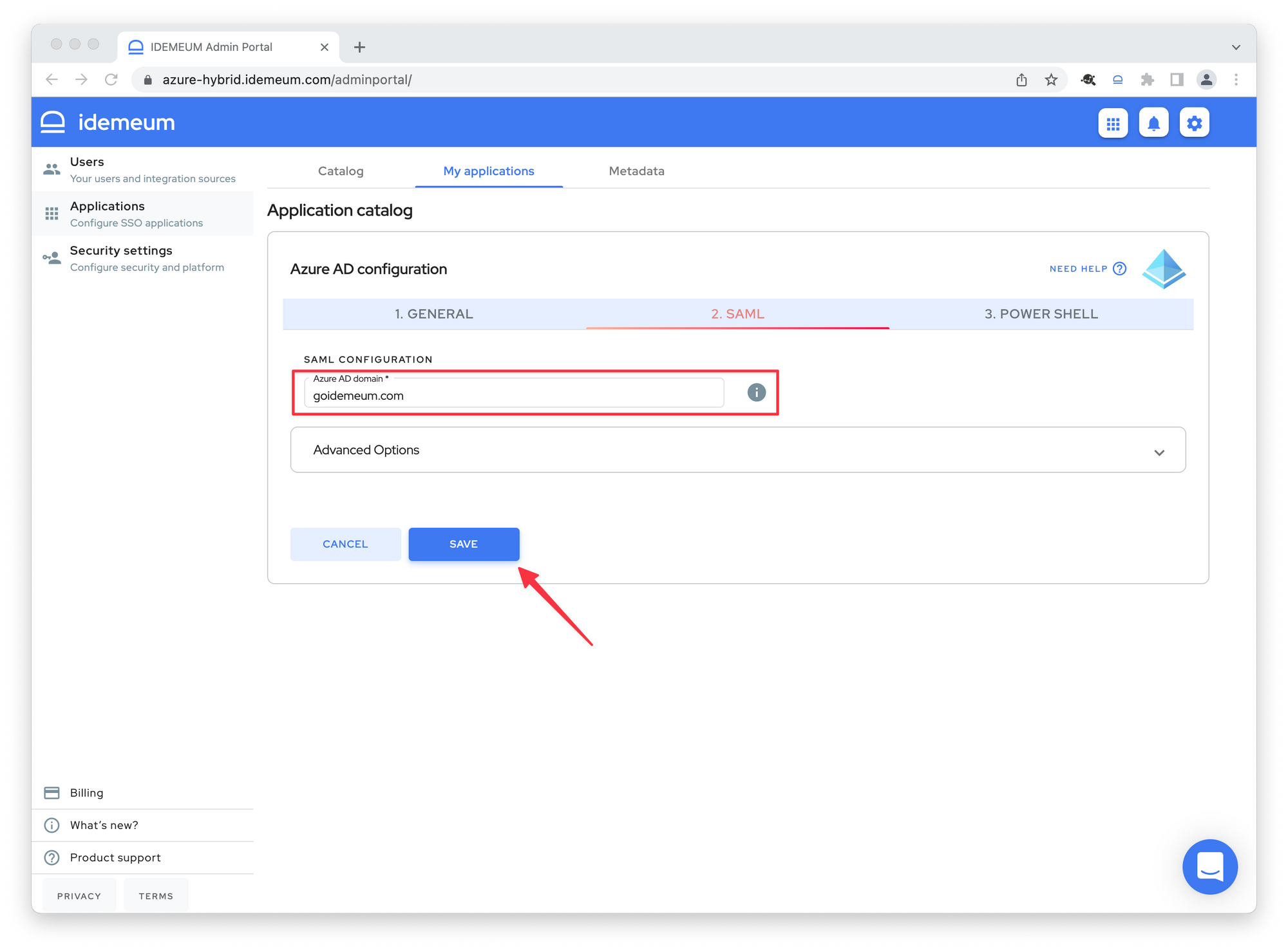
- Click SAML and enter your Azure AD domain that you want to federate with idemeum
- Click Save
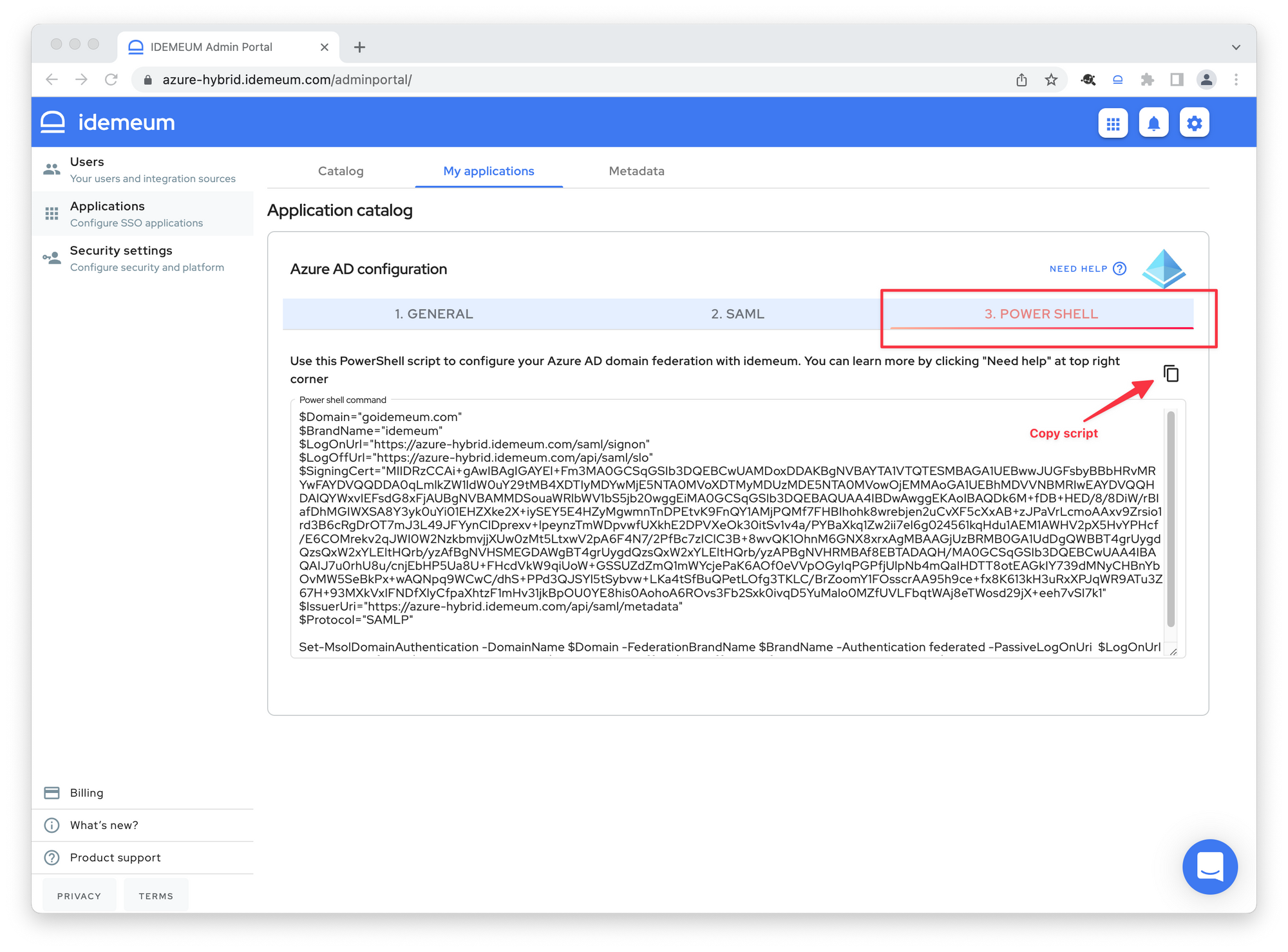
- Now click on the PowerShell section to get the script automatically generated for your idemeum tenant. You can copy that script as you will need it later when setting up federation with Azure AD.
- Launch PowerShell on a Windows machine
- Install MSOnline PowerShell module if you have not already.
Install-Module MSOnline- If you have error that module is not available you need to make sure that you are using latest version for TLS. You can try the following command to fix the error.
[Net.ServicePointManager]::SecurityProtocol = [Net.SecurityProtocolType]::Tls12
- Connect to MSOnline service. You will need to authenticate with your Azure AD admin credentials
Connect-MsolService
- You can check your existing domains and their federation settings
Get-MsolDomain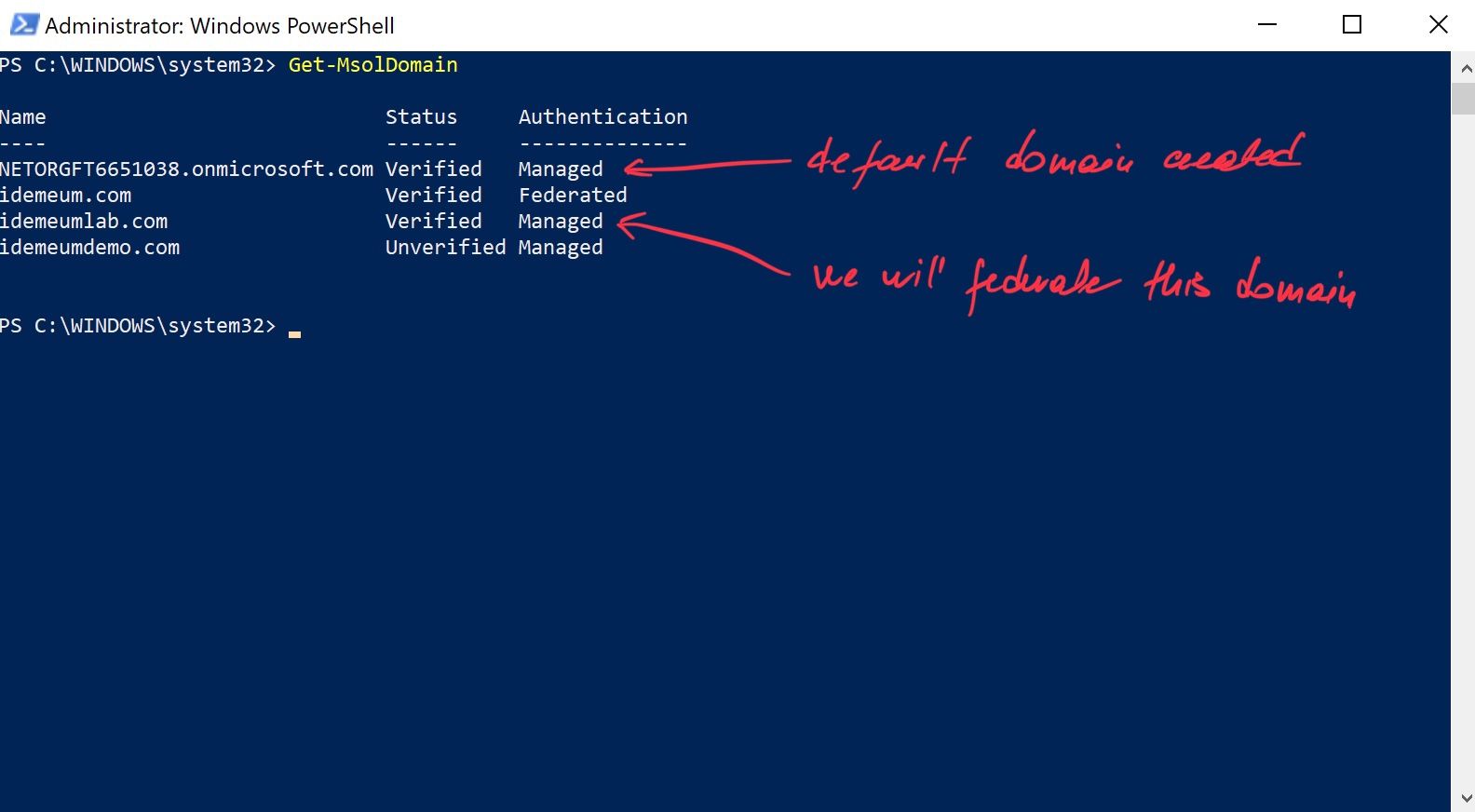
- If the current setting for your domain is federated, you will need to first convert domain back to managed setting. You can use the following command to revert it back to managed.
Set-MsolDomainAuthentication -DomainName <yourdomain> -Authentication managed- Now take the script that you obtained from idemeum and execute it in PowerShell by copy pasting it.
- Verify that the settings are successfully configured for your domain.
Get-MsolDomainFederationSettings -DomainName <your domain here> | format-list *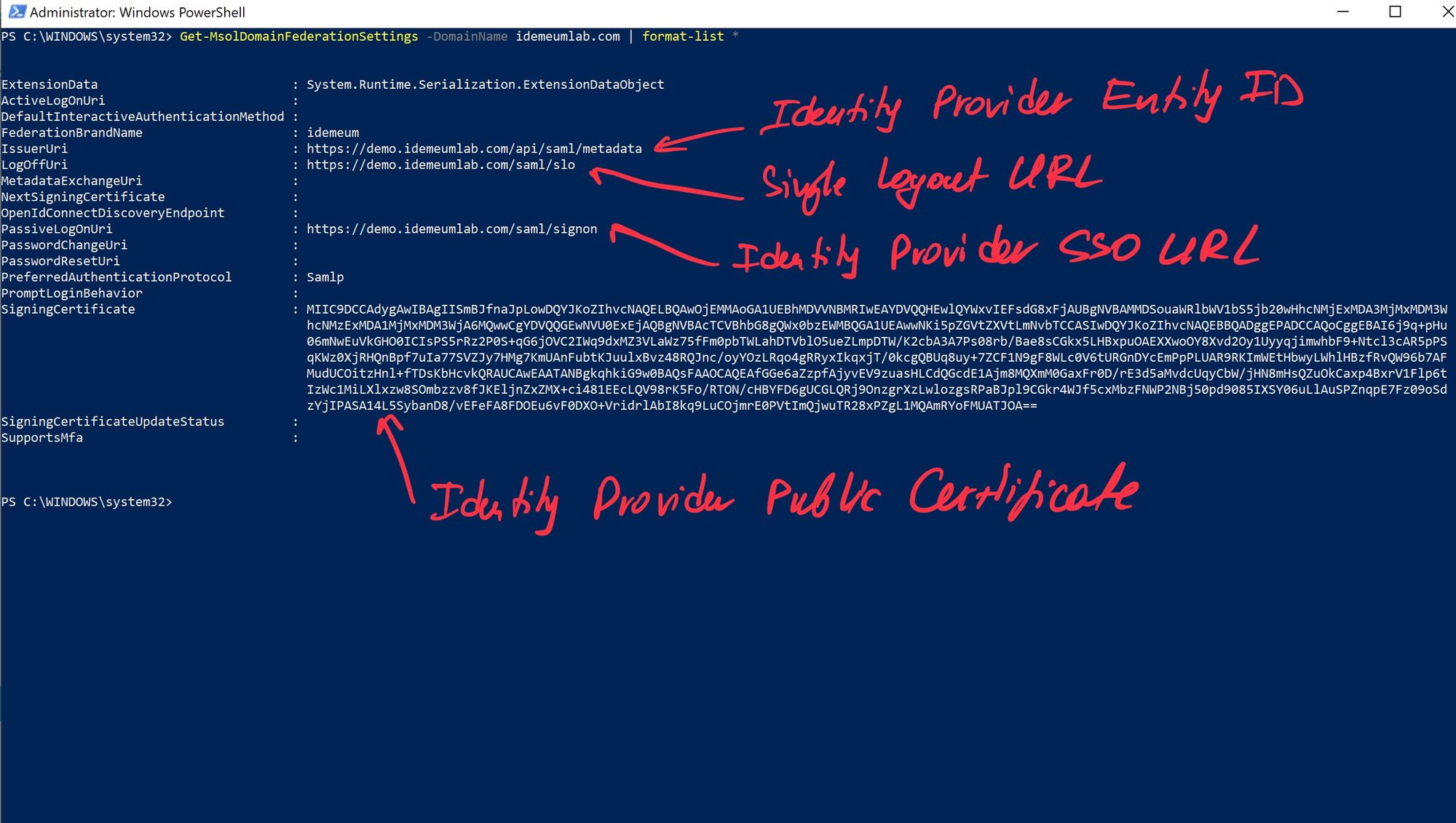
Create new users
For Cloud only deployment you can create users directly in idemeum and they will be synced to Azure AD.
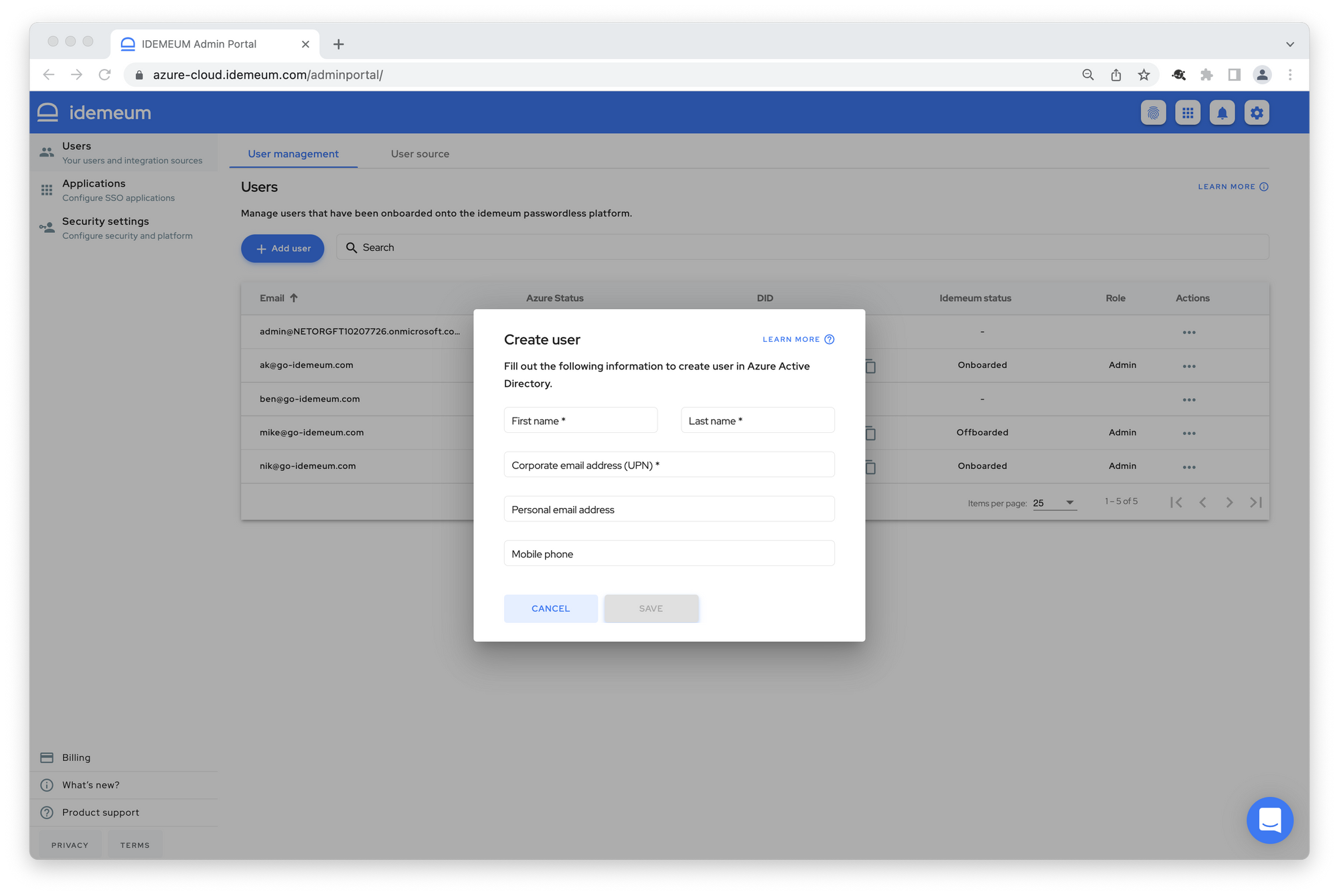
- Navigate to Users -> User management section in admin portal
- Click Add user
- You will be able to enter First name, last name, and user principal name (i.e. corporate email address). Make sure you enter personal information for the user so that user can be onboarded using those personal claims.
- Once you click Save user will be synchronized to Azure AD.
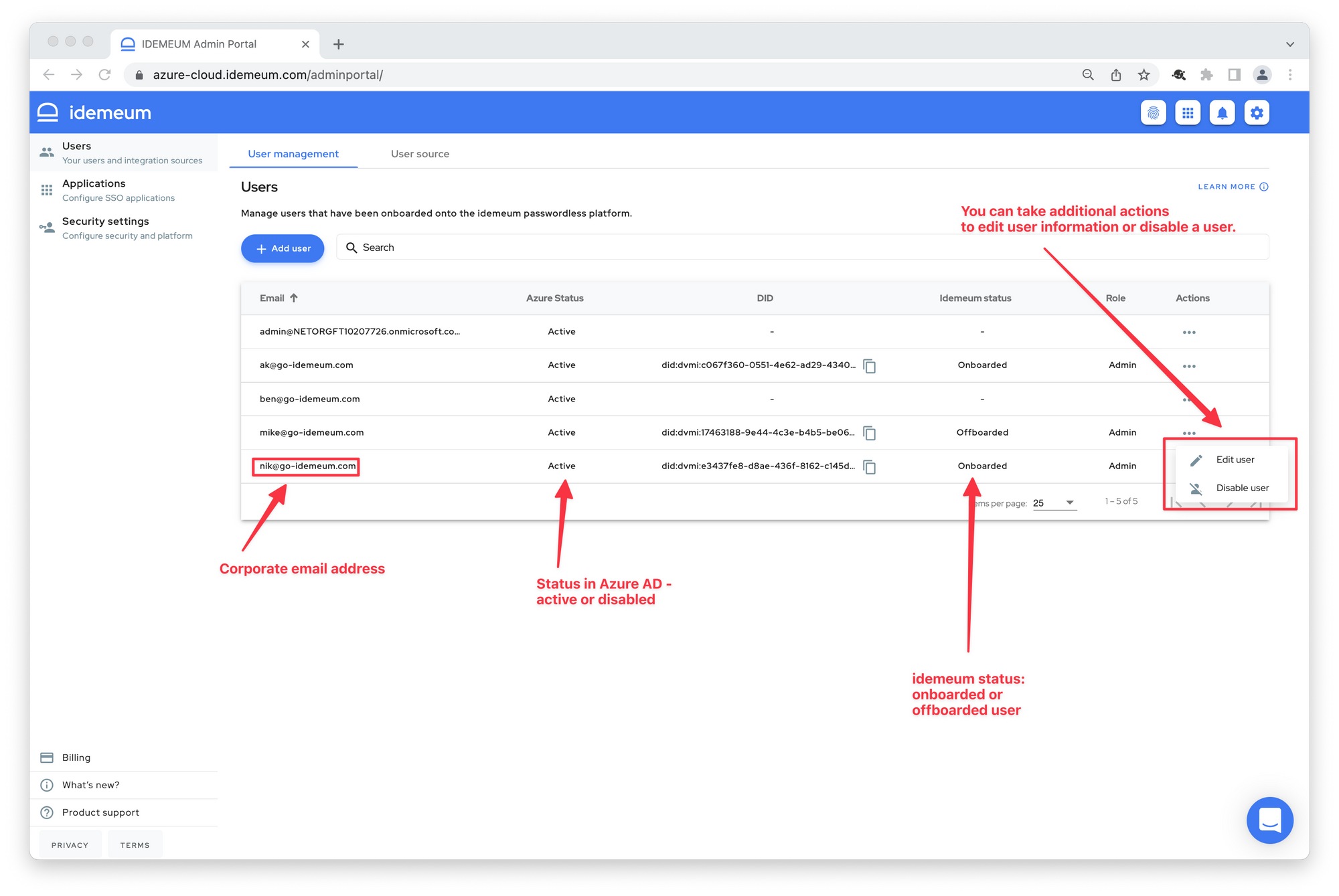
Here is some additional information about the user management capabilities for Azure AD cloud deployment.
For Hybrid deployment the source for your users is the Active directory on-premises. Therefore you will need to be creating users in on-premises Active directory.
Once you create your users in Active directory they will be synced to Azure AD by Azure AD Connect. Typical sync interval is 30 minutes. You can trigger manual sync using the following command.
Import-Module ADSync
Start-ADSyncSyncCycle -PolicyType Delta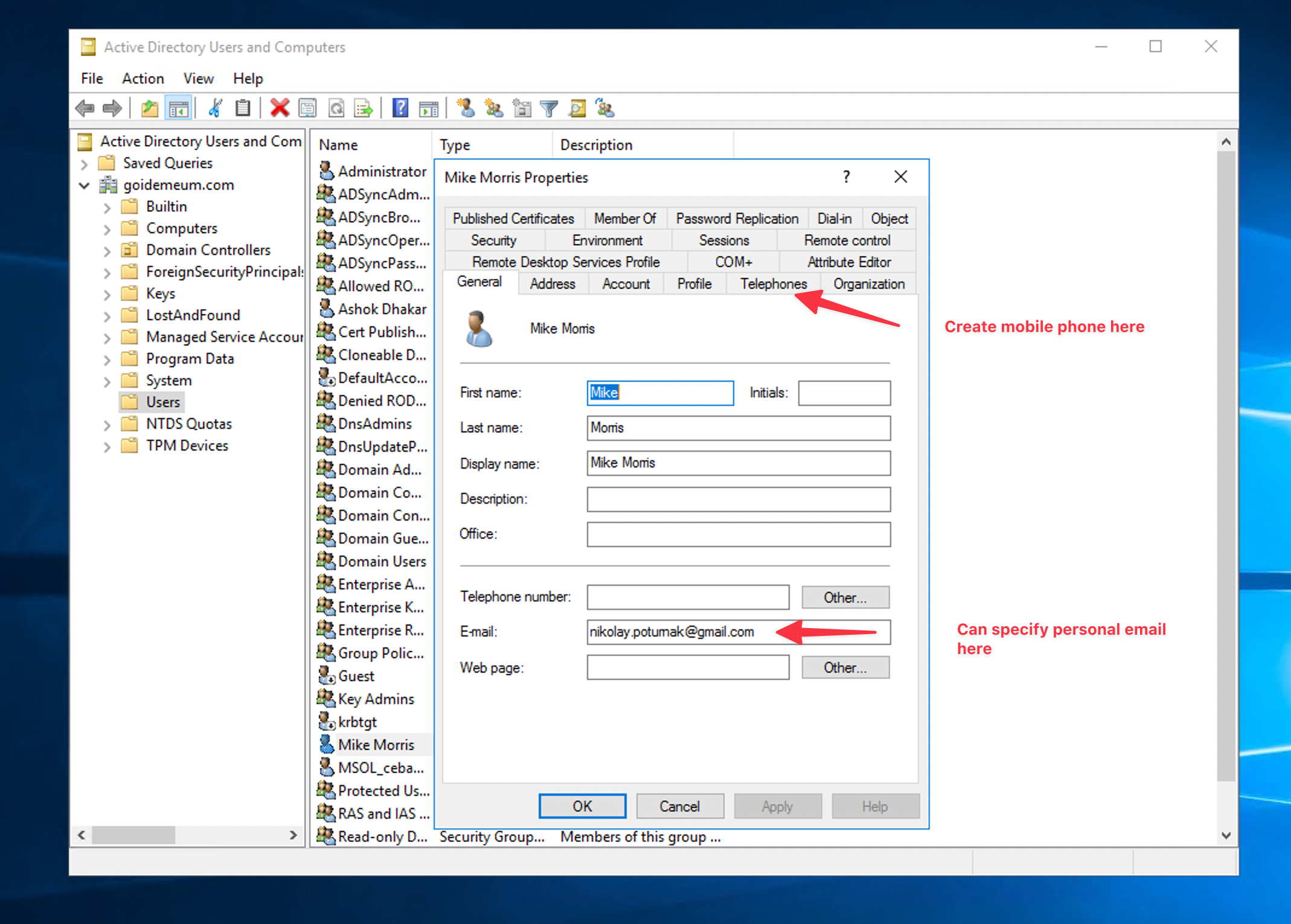
User offboarding
For Hybrid deployment you need to off-board user in your Active Directory. Once you disable the user, information will propagate to Azure AD and subsequently to idemeum. idemeum checks for disabled user every 4 hours by default. Once disabled user is detected, user will no longer be able to access company resources.
For Cloud deployment you can off-board user directly in idemeum. Navigate to Users -> User management menu in the admin portal, and you will be able to directly off-board user.
Test login flow
Now you can test login flow by going directly to Office 365 and login with passwordless SSO.
- Open browser window and navigate to
portal.office.com - Enter the email address of the account that you would like to sign into. Once you do that you will be redirected to idemeum for login.

